The Squid configuration screen in IPCop is very easy to follow and you can get away with clicking a couple of boxes for a basic configuration.
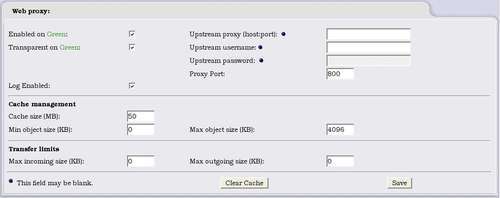
In this example we have only a Green interface present; we can, however, enable the proxy on all other interfaces—except Red, which is the internet connection.
The first step is quite obvious; we enable the proxy on the interfaces we need it on by clicking the first checkbox and then choosing the port the proxy listens on (800 by default in IPCop—although Squid usually runs on port 3128). We can also check the Log Enabled box, which is interface non-specific, so we either log all or log none. It's a good idea to enable this if we want to monitor the proxy at some point. We can also chain this proxy through one provided by our ISP for example by configuring the Upstream options, which would be provided by the ISP or other proxy service provider. The host port to connect to, and a user name and password may be necessary.
Transparency...