Tags allow you to attach a marker to the fields and event types in Splunk. You can then search and report on these tags later. Let's attach a tag to a couple of users who are administrators. Start with the following search:
sourcetype="impl_splunk_gen" | top user
This search gives us a list of our users such as ronnie, tuck, jarde, shelby, and so on:

Let's say that in our group, shelby and steve are administrators. Using a standard search, we can simply search for these two users like this:
sourcetype="impl_splunk_gen" (user=shelby OR user=steve)
Searching for these two users while going forward will still work. However, if we search for the tag value, we can avoid being forced to update multiple saved queries in the future.
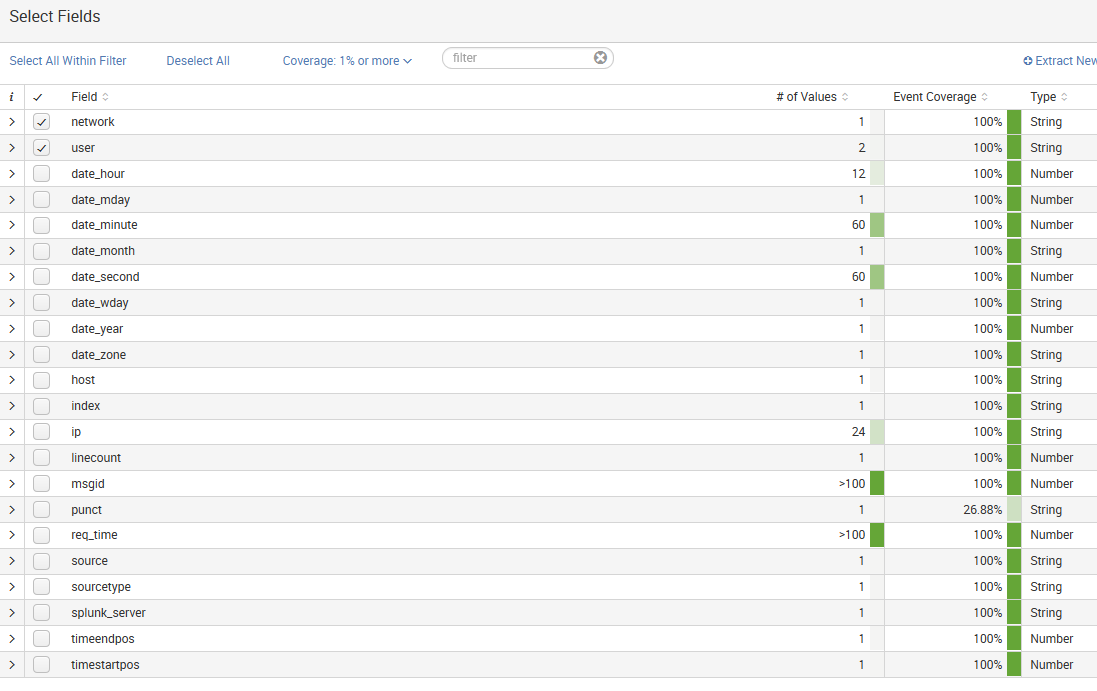
To create a tag, we first need to locate the field:
If the user field isn't already visible, click on it in the field picker, and then click on Select and show in results:
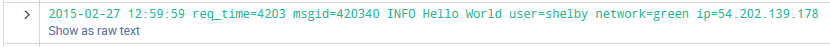
From our listed events, you can select an event and click on the arrow...



