Cybersecurity is the foster child of the internet. With the proliferation of networks and networks of networks, information (data) and intelligence (software programs and applications) stored in a given network domain became vulnerable to unauthorized access. To prevent such access and its consequences, cybersecurity and information security became an indispensable discipline. Cybersecurity can be generally defined as a technology stack of processes, protocols, and practices to protect computing systems (servers, application endpoints), data, and networks from unauthorized access, malicious attacks, and other forms of intentional and unintentional damage.
Securing the Industrial Internet can be considered as a superset of cybersecurity, since now we are talking about protecting cyber-physical systems.
A cyber-physical system (CPS) refers to any network-connected instrumentation that also interacts with the physical world. Consider the example of a thermostat that's connected to a data network. In the industrial context, a common example of a cyber-physical system is an industrial control systems or ICS. An ICS is a general term used to describe a wide variety of control systems and instrumentation that's used to control industrial processes. This ranges from small panel-mounted controller modules with few control loops to several geographically distributed controllers.
Large-scale ICS is usually deployed using supervisory control and data acquisition (SCADA) systems, or distributed control systems (DCS) and programmable logic controllers (PLCs). All systems receive data from remote sensors that measure process variables (PVs), compare these with desired set points (SPs), and derive command functions that are used to control a process through the final control elements (FCEs), such as control valves.
When a CPS is connected to an external network (let's say to a centralized cloud infrastructure), we can refer to it as a cyber-physical IoT. The following diagram is a generalization of an ICS or a cyber-physical system. The system could be controlling engine performance and acceleration in an automobile, or the temperature-based controls in a power grid:
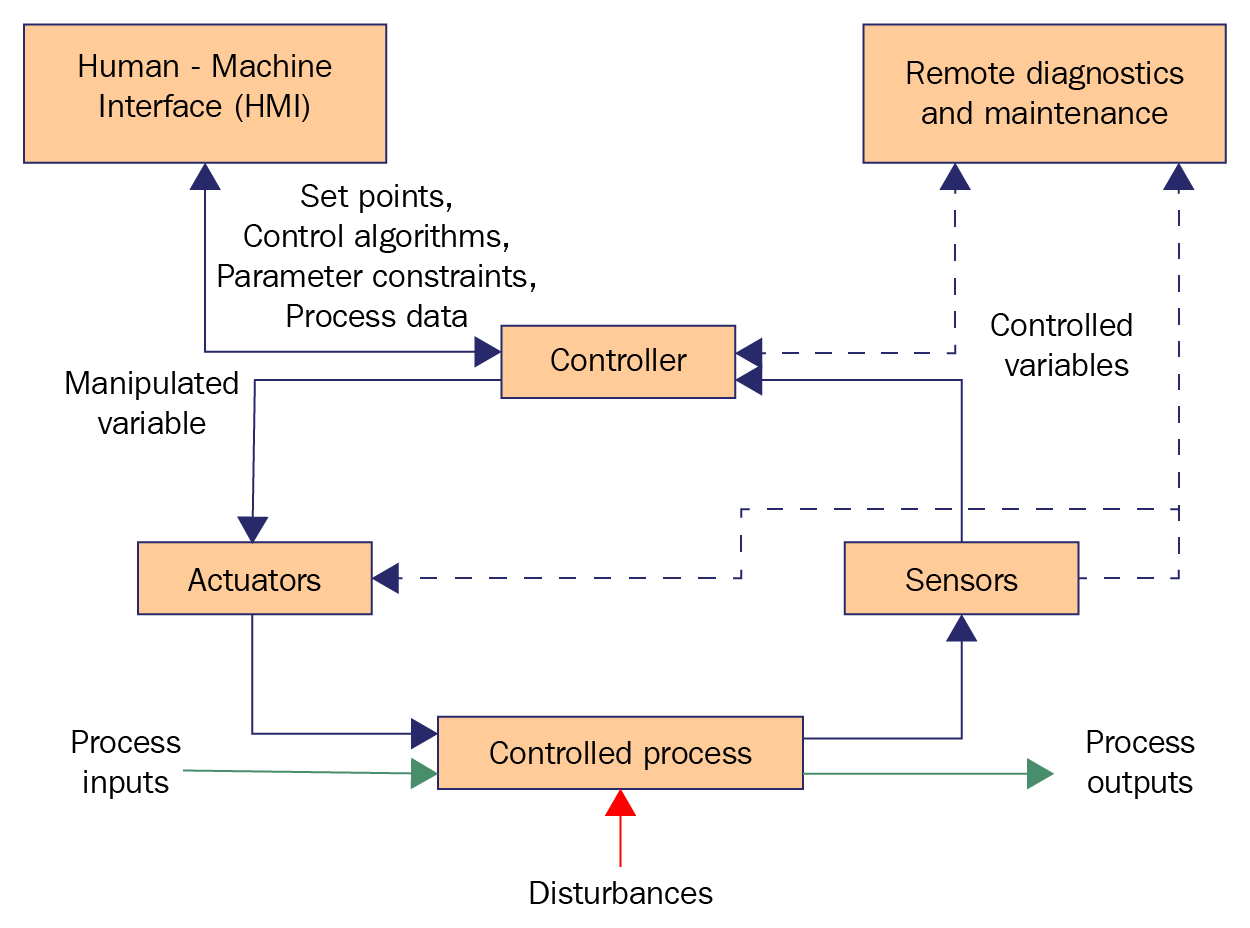
Figure 1.3: Industrial control system (ICS) functional flow diagram; Source: (NIST-800-82r2)
In the case of cybersecurity, the prime focus is to protect the data itself. Data privacy and identity protection are the top priorities. In the case of cyber-physical security, visibility into the controls is important. For example, if a temperature sensor in a power generation plant is hacked remotely, it can incorrectly output very high temperature values, which would cause the control system to shut down the entire power plant. In the reverse case, that is, if the sensor output is much lower than what it should be, the control action may result in much more dangerous consequences.
General characteristics of any CPS/ICS system include:
- Ability to interact with the physical environment over a communication channel to receive inputs (for example, temperature) and/or feedback. In this case, unlike a cyberattack, an attacker can cause damage without breaking into the system by remotely triggering a set of physical actions. These actions can be sensed, causing the CPS to exhibit unexpected behavior. This highlights the need to secure the communication channel and the end devices.
- Management and control are typically distributed.
- Uncertainty regarding readings, status, and trust.
- Involves real-time control loops with deterministic performance requirements.
- Can be geographically spread over a large area, with components in locations that lack physical security.
These characteristics render cyber-physical security more complex than cybersecurity. In CPS, due to environmental interactions, a security breach has physical safety implications.
This necessitates cyber-physical control systems being inherently resilient. A control system is characterized as resilient when it can maintain state awareness and an accepted level of steady state behavior (operational normalcy) when exposed to abnormal conditions, which include intentional and unintentional errors, malicious attacks, and disturbances (RIE-GERT).



