One of the major aspects of user authentication is monitoring the users of the system. There are various ways to keep track of all the successful and failed login attempts made by a user in Linux.
The Linux system maintains a log of all login attempts by different accounts in the system. These logs are all located at /var/log/.
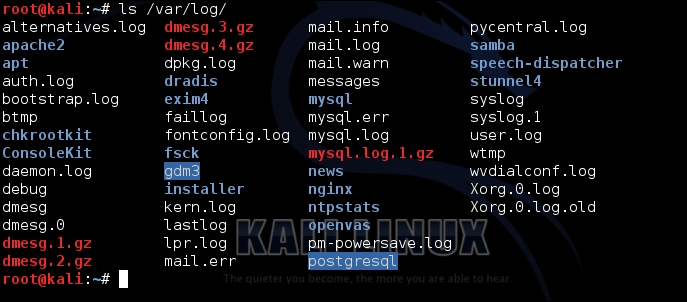
Linux has many ways to help an administrator to view the logs, both through a graphical and command-line method:
If we want to check the incorrect login attempts for a particular user, such as root, we can do so by using this command:
lastb root
To see the log using the terminal, we use the
dmesgcommand. This command displays the buffer of Linux kernel's message stored in memory, as shown below:
If we wish to filter the above output to only show the log related to a USB device, we can do so by using
grep:
Instead of viewing all the logs, if we only wish to view the 10 most recent logs in a particular log file...