Noooo, it's that annoying pop-up screen again!
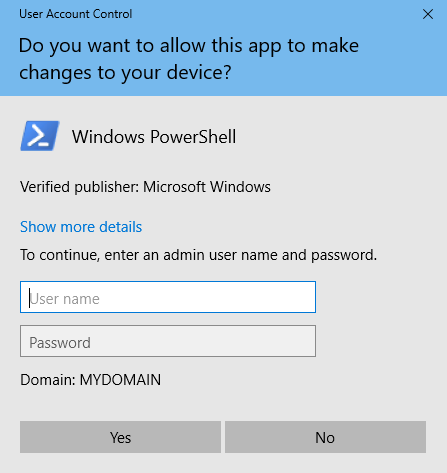
This little credential prompt seems so annoying, yet it can save your bacon. UAC is an invaluable tool that halts installation processes, or the launching of applications into a mode that has elevated privileges. For example, I tried to open an administrative PowerShell prompt and was presented with the preceding screenshot.
UAC is an in-your-face reminder that something big is about to happen. When an application installer gets launched, you want to make sure it is something you actually intended to install, right? I have witnessed webpages try to launch malicious installers on computers, only to be stopped by UAC. By simply pressing No on this screen, you stop whatever activity was about to happen. There is also plenty of danger in opening up an administrative window, so Windows uses UAC to double-check...



