In this chapter, we discussed multiple security controls for a cloud service to meet the industrial grade of trustworthiness.Table 6.2 provides an assessment matrix that can be used in conjunction with cloud security standards compliance to evaluate the security readiness of an IIoT cloud service:
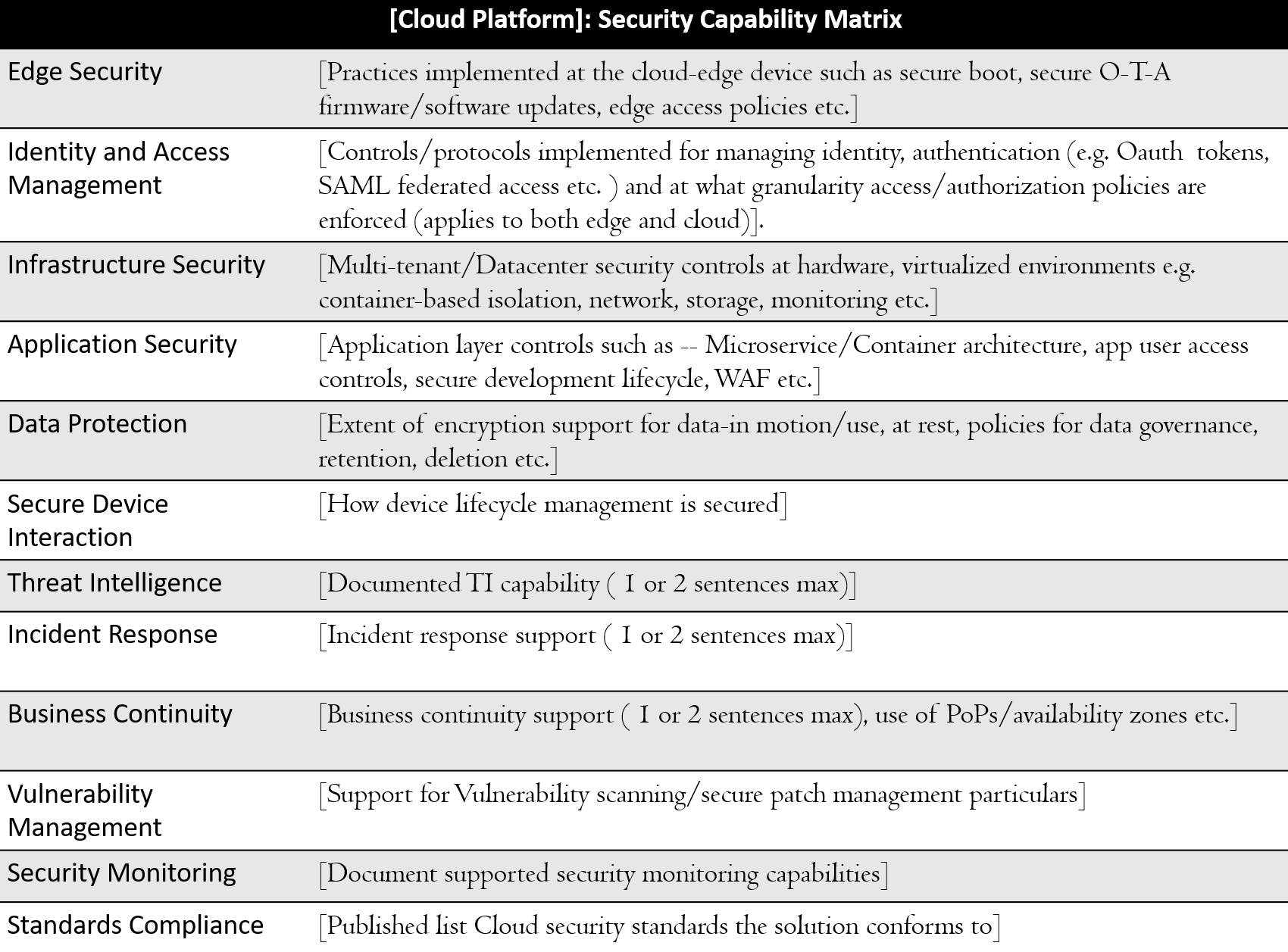
Table 6.1: Cloud security assessment matrix
As an illustration of the use of the table, Table 6.3 shows the mapping of the published security capabilities (at the time of writing) of the Predix IIoT platform in the security assessment matrix (PDX-BRF):

Table 6.2: A sample cloud security assessment Matrix



