Go right ahead and connect your GPS gadget to the USB port. Most GPS units appear to Linux as serial ports with device names starting with tty then commonly followed by ACM0 or USB0. Type in the following command and focus on the last line:
pi@raspberrypi ~ $ dmesg -T | grep tty
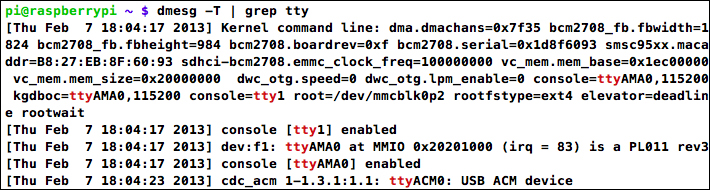
USB GPS receiver identifying as ttyACM0
The first couple of lines talk about the serial port built into the Pi (ttyAMA0). On the last line, however, a USB device is identified which is most likely our GPS unit and will be accessible as /dev/ttyACM0. We can confirm that it's a GPS by trying to read from it using the following command, where [XXXX] should be replaced by the name of your device:
pi@raspberrypi ~ $ cat /dev/tty[XXXX]
A GPS conforming to the NMEA standard will start flooding your screen with sentences beginning with a code such as $GPGGA followed by comma-separated data (see http://aprs.gids.nl/nmea/ if you're curious about those messages). Even if your GPS outputs...