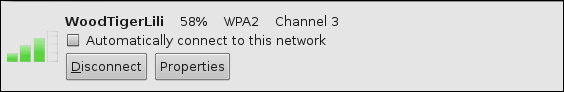
It is disturbing that we continue to see networks using the Wired Equivalent Privacy (WEP) algorithm. We will get into the weaknesses of WEP and show how easy it is to obtain the WEP key for an attacker and also for you if you are working with your own network or have written the authorization to test someone else's network. There is absolutely no reason you or anyone else should be using WEP to protect a wireless network. Now that you know how to get your card to work, you can click on a network and connect to it if you like by clicking on the Connect button. An example of a connection to the WoodTigerLili network is shown in the following screenshot:
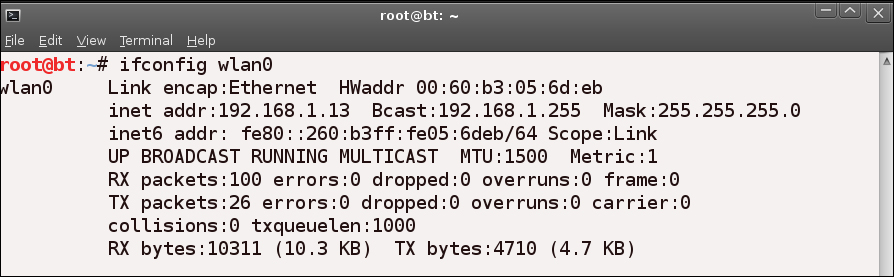
Once we are connected, we can treat this like any other wireless connection. You can verify that it is connected by entering the ifconfig wlan0 command in a terminal window:
root@bt:~# ifconfig wlan0
The output of a connected adapter is shown in the next screenshot:
As you may have noticed, this is just...