Many times, you will not be able to intercept an application's HTTPS traffic, even after installing Burp Suite CA certificate on the device. Nowadays, many applications implement SSL pinning, where an application checks the server's certificate against a known copy of that certificate. This prevents the usage of any untrusted certificate that is being used for man-in-the-middle (MITM) attacks.
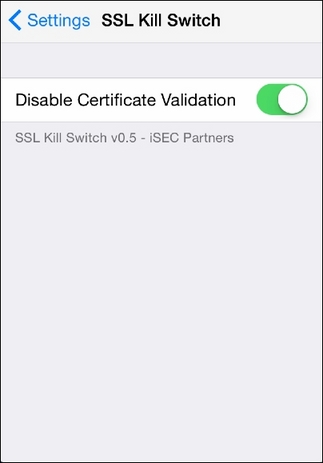
You can bypass SSL pinning by using tools such as SSL Kill Switch. However, note that this is available only for jailbroken devices. I would encourage you to go further and study from its wiki on how it helps in bypassing SSL verification.
It comes as a Debian package and once you install it on iDevice, you will need to enable the switch, as shown in the following:
I would encourage you to download popular apps from App Store and check whether you can view the application's traffic in plain text. Make sure that you just observe the traffic and not perform any attacks, as legal permission...