Sometimes we need to remain untraceable while performing a pentest activity. Proxychains helps us by allowing us to use an intermediary system whose IP can be left in the logs of the system without the worry of it tracing back to us.
Proxychains is a tool that allows any application to follow connection via proxy such as SOCKS5, Tor, and so on.
Proxychains is already installed in Kali. However, we need a list of proxies into its configuration file that we want to use:
- To do that we open the config file of proxychains in a text editor with this command:
leafpad /etc/proxychains.confThe following screenshot shows the output for the preceding command:
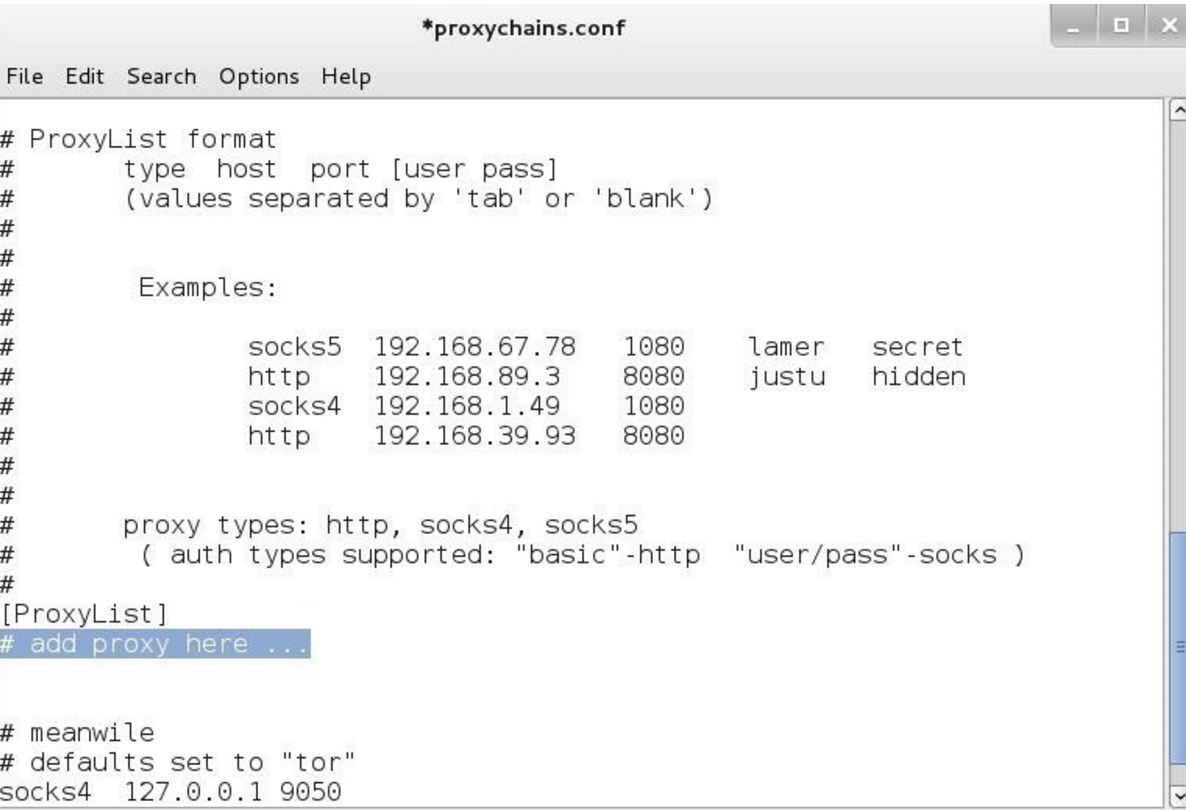
We can add all the proxies we want in the preceding highlighted area and then save.
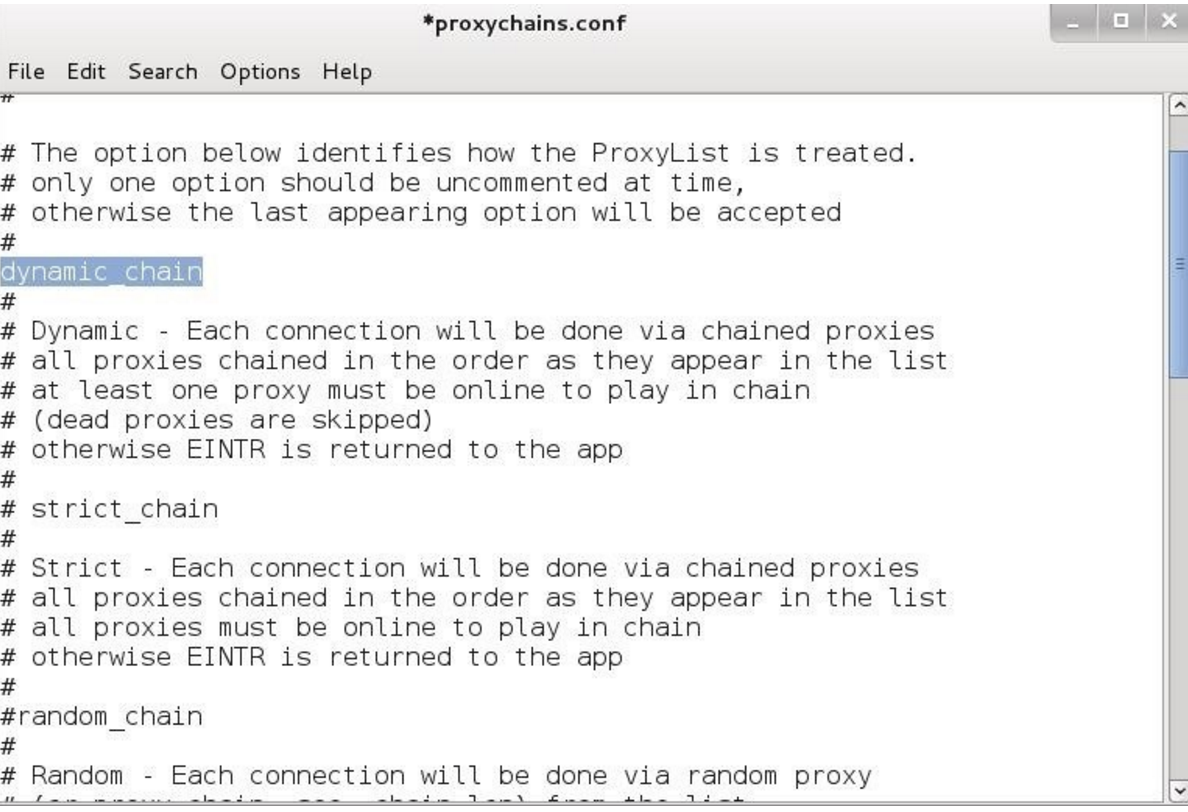
Proxychains also allows us to use dynamic chain or random chain while connecting to proxy servers.
- In the config file uncomment the dynamic_chain or random_chain:
To learn about tor follow the given steps:
- To use proxychains with tor we first need to install tor using the following command:
apt-get install tor- Once it is installed we run tor by typing
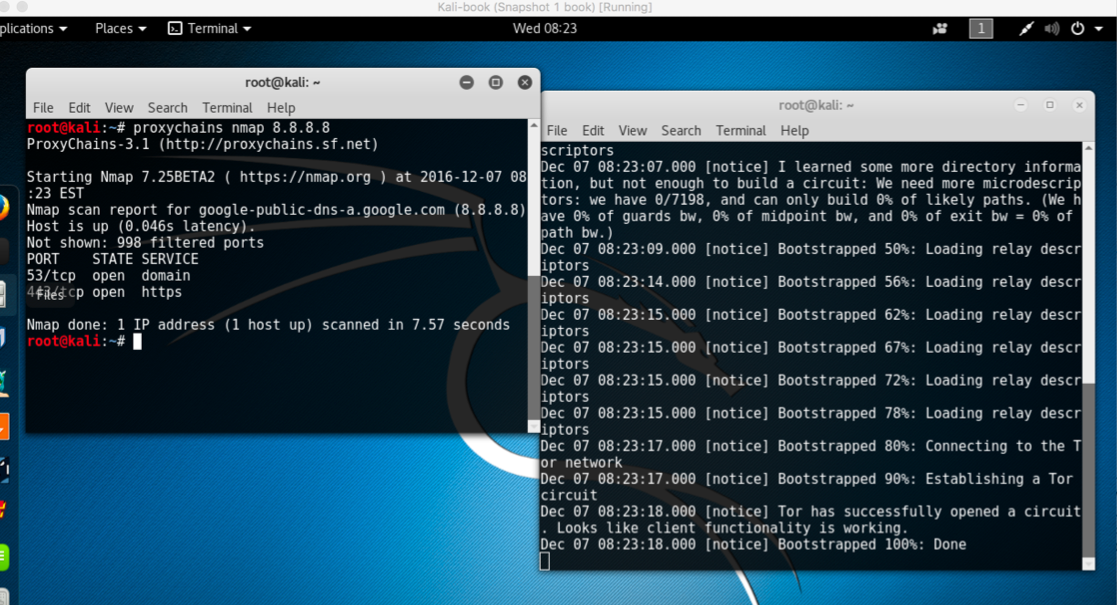
torin the Terminal. - We then open another Terminal and type the following command to use an application via proxychains:
proxychains toolname -argumentsThe following screenshot shows the example of the preceding commands: