The folks at https://www.kali.org/ and Offensive Security (the team responsible for Kali and its predecessor, Backtrack Linux) have made Kali one of the most versatile distributions. In addition to providing flavors for a staggering number of platforms and architectures, they made it simple for us to pick and choose subsets of the full distribution for our needs. The base image for ARM platforms (such as the Pi) include a pretty small subset of applications, and it is likely that we will need a few more to meet our goals. These subsets of tools, called metapackages, help us quickly grab the software packages and their dependencies for the job. The more pertinent metapackages to our work can be seen in the following image:
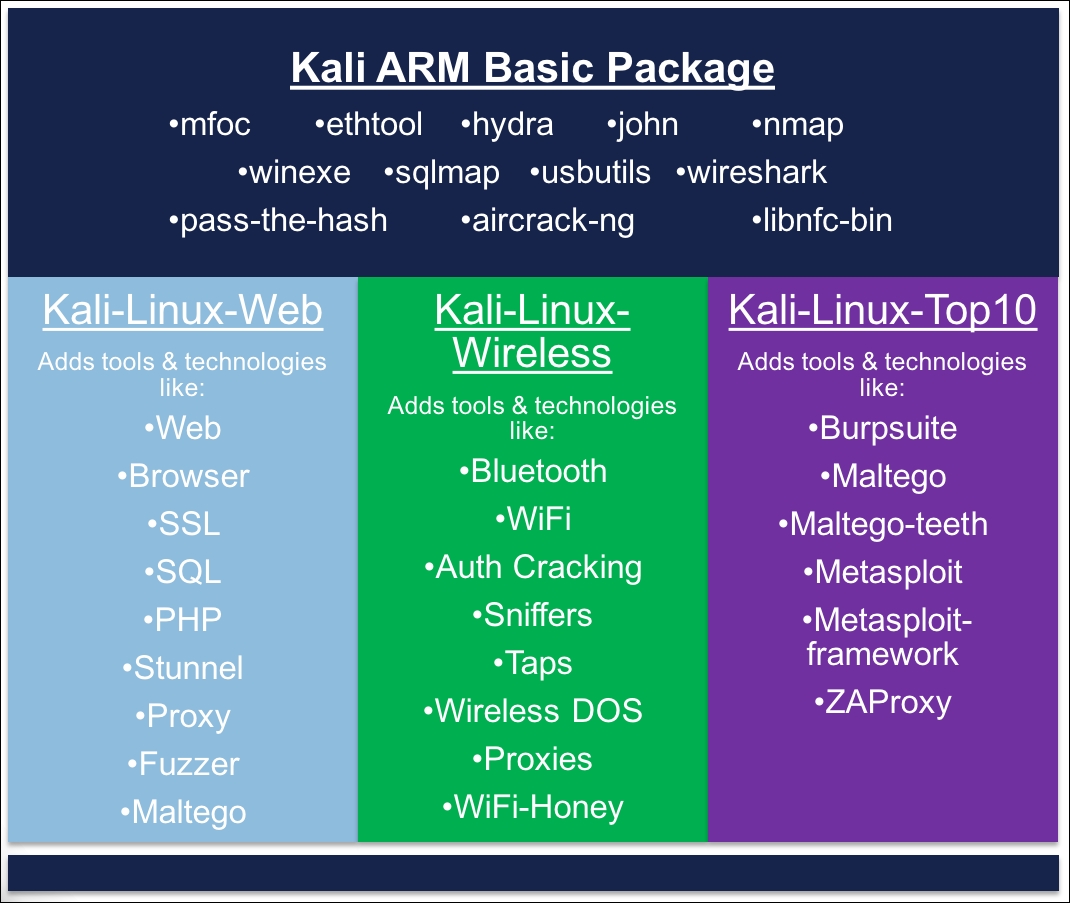
Other metapackages (GPU, Forensics, PWTools, VoIP, and SDR) do exist, but are of limited use in our penetration testing use case. These tool sets would more likely be enlisted on our C&C server or a more fully-featured...



