Let us start with a basic setup guide for Armitage. We will cover Armitage setup in Windows and BackTrack in Linux. Armitage comes pre-installed in recent versions of BackTrack. To set up Armitage on Windows, we can download the ZIP file from its official web page
http://www.fastandeasyhacking.com/download
Let us start with setting up Armitage in BackTrack.
Armitage will be pre-installed in BackTrack 5 R2. It can be launched by clicking on Applications on the desktop and then navigating to Backtrack | Exploitation tools | Network Exploitation tools | Metasploit framework | Armitage.
You will see a GUI that will ask you to set up the connection. It will have the default username and password as
msfandtestrespectively. You can keep the DB driver aspostgressqland finally the DB connect string asmsf3:"8b826ac0"@127.0.0.1:7175/msf3: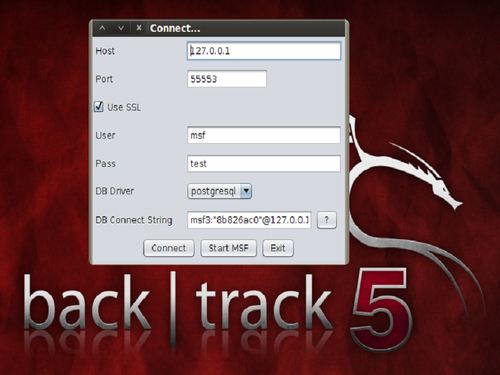
Once these default settings are done, we can start the Armitage GUI by clicking on Start MSF.
To set up Armitage...