The ls command is used to list files in a directory, and it is similar to the dir command in DOS. This command can be used with various parameters to give different results.
Since the ls command is a built-in command of Linux, we don't need to install anything else to use it.
Now, let's take a look at how we can use ls in different ways to get a variety of results by just following these given steps:
To take a look at the simple listing of files in a current directory, type
ls:
To get more information about the files and directories listed using the
lscommand, add a type identifier, as shown here: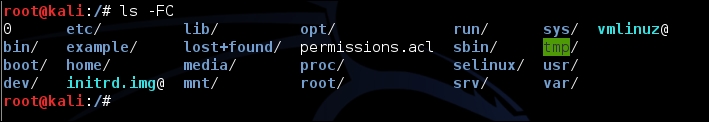
When the preceding identifier is used, the executable files have an asterisk at the end of the name, while the directories have a slash, and so on.
To check out details of files, such as the creation dates, owners, and permissions, run the command with the
lidentifier, as shown here:
To find a listing of all the hidden...