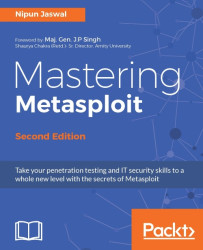
Core meterpreter commands are those that are available on most exploited systems using a meterpreter payload and that provide the basic core functionalities for post exploitation. Let's get started with some of the most basic commands that will help you get started with post-exploitation.
We can always refer to the help menu to list all the various commands that are usable on the target by issuing help or ? as shown in the following screenshot:
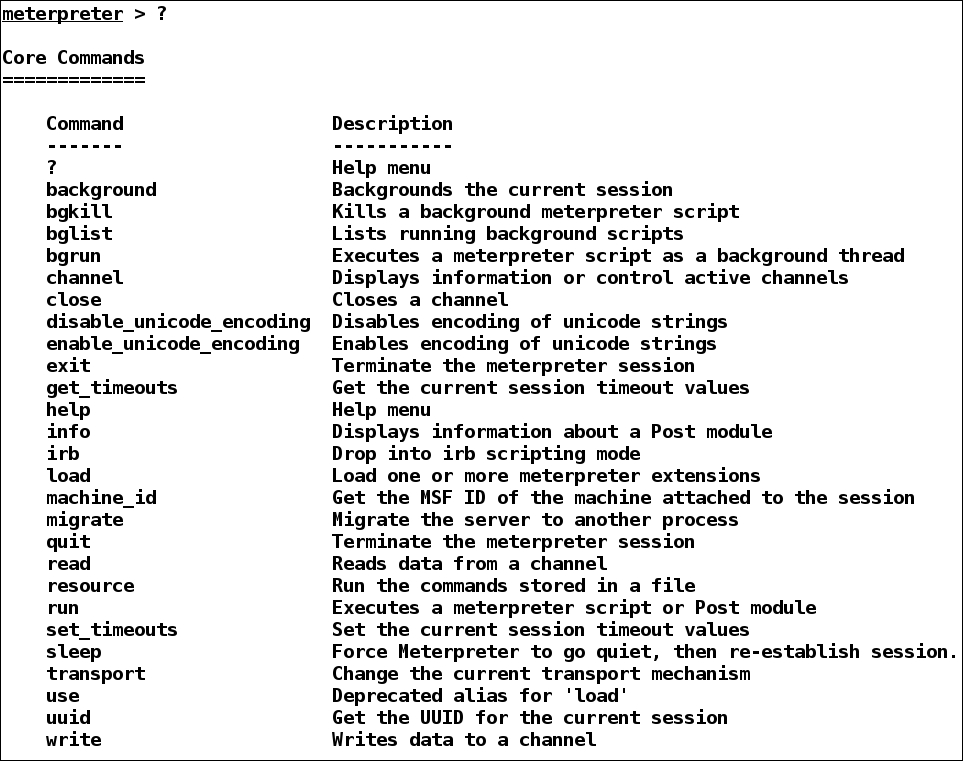
While carrying out post exploitation, we may run into a situation where we need to perform additional tasks, such as testing for a different exploit or running a privilege escalation exploit. However, in order to achieve that we need to put our current meterpreter session in the background. We can do this by issuing the background command, as shown in the following screenshot:
We can see in the preceding screenshot that we successfully managed to put our session in the background and...