For our next threat modeling exercise, we will examine IoT mobile applications for our DVR system. This DVR system (like many others in IoT) has several mobile applications available developed by resellers and different OEMs. For demonstration purposes, we will only threat model one Android and one iOS application.
Since we have the majority of our data flow diagrams created from previous recipes, we will continue to use the same Microsoft Threat Modeling Tool for this recipe.
Similar to our last couple of recipes, we will jump right to creating a data flow diagram which includes all known assets for the mobile applications. The following is the data flow diagram for the mobile applications:
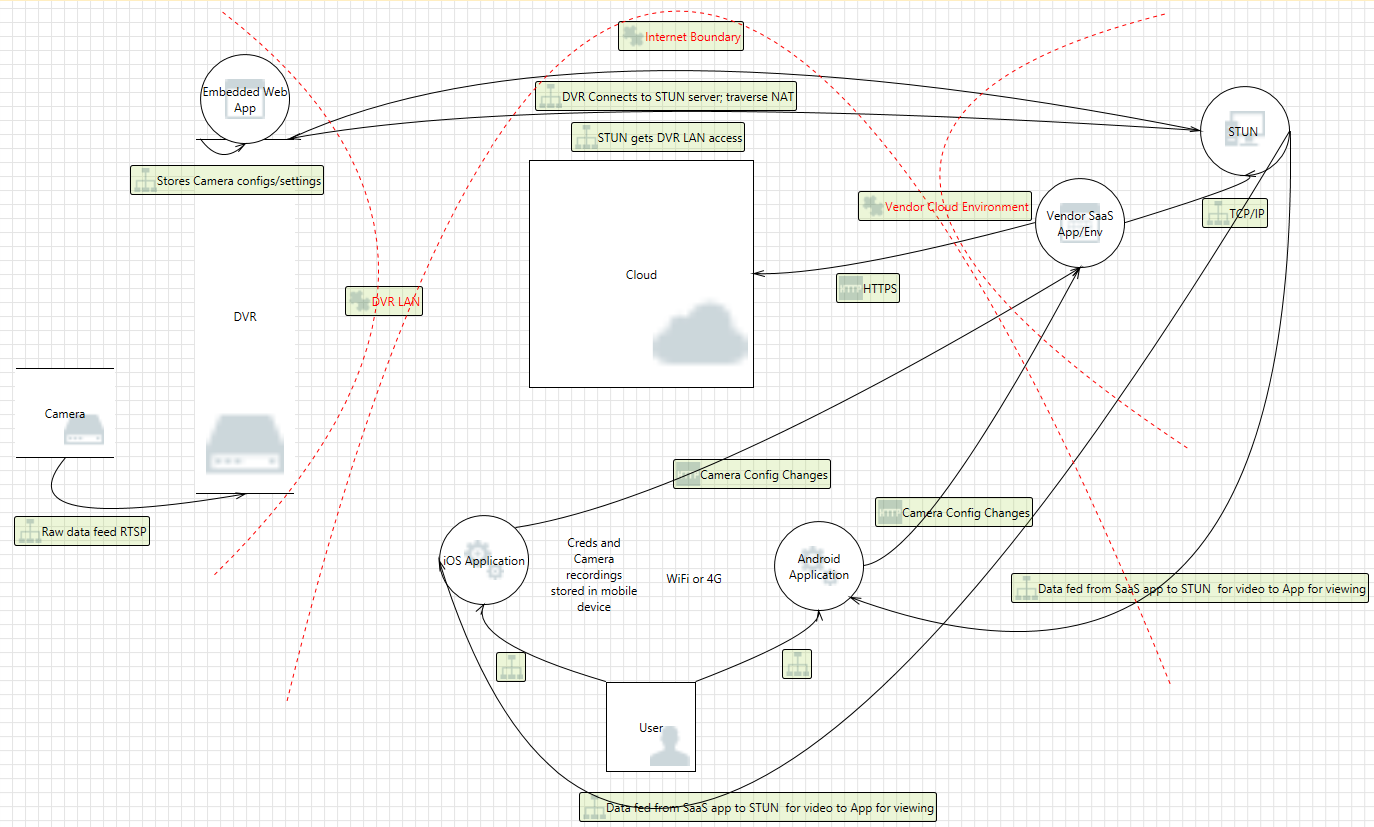
We can see that the applications contact the third-party vendor cloud environment each time in order to view account details and camera feeds. This also occurs when the user is in the same...



