Let us begin! We will set the access point up to use Open Authentication with an SSID of "Wireless Lab".
Follow these instructions step-by-step:
Power on the access point and use an Ethernet cable to connect your laptop to one of the access point's Ethernet ports.
Enter the IP address of the access point configuration terminal in your browser. For the DIR-615, it is given to be 192.168.0.1 in the manual. You should consult your access point's setup guide to find its IP address. If you do not have the manuals for the access point, you can also find the IP address by running the
route –ncommand. The gateway IP address is typically the access point's IP. Once you are connected, you should see a configuration portal which looks like this:
Explore the various settings in the portal after logging in and find the settings related to configuring a new SSID.
Change the SSID to Wireless Lab. Depending on the access point, you may have to reboot it for the settings to change:

Similarly, find the settings related to Authentication and change the setting to Open Authentication. In my case, the Security Mode configuration of None indicates that it is using Open Authentication mode.
Save the changes to the access point and reboot it, if required. Now your access point should be up and running with an SSID Wireless Lab.
An easy way to verify this is to use the Wireless Configuration utility on Windows and observe the available networks using the Windows Laptop. You should find Wireless Lab as one of the networks in the listing:
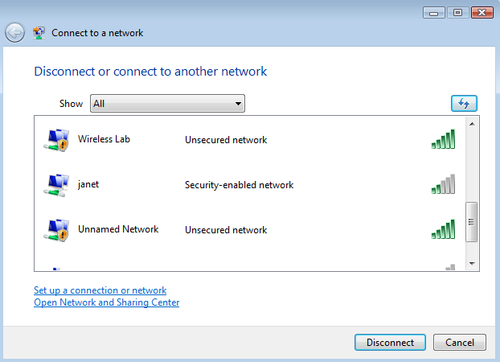
We have successfully set up our access point with an SSID Wireless Lab. It is broadcasting its presence and this is being picked up by our Windows laptop and others within the Radio Frequency (RF) range of the access point.
It is important to note that we have configured our access point in Open mode, which is the least secure. It is advisable not to connect this access point to the Internet for the time being, as anyone within the RF range will be able to use it to access the Internet.
Play around with the configuration options of your access point. Try to see if you can get it up and running using encryption schemes such as WEP and WPA/WPA2. We will use these modes in the later chapters to illustrate attacks against them.