AD is an identity service developed by Microsoft for users and machines. AD has a domain controller, also known as Active Directory Domain Service (AD DS), which stores the user's and the system's information, their access credentials, and their identity. The following diagram illustrates a simple flow of the necessary authentication process:
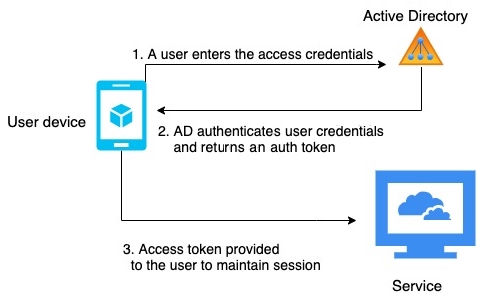
As shown in the preceding diagram, the user login is managed by AD or any resource on the domain networks. Users first send the request to the domain controller with their credentials and communicate with the Active Directory Authentication Library (ADAL). The ADAL verifies the user credentials and sends back an access token with a continuous session for the requested service.
LDAP is the standard protocol that handles the tree-like hierarchical structure of information stored in directories. Active Directory Lightweight Directory Services (AD LDS) provides an LDAP interface to the directory of users and systems...