Joint Test Action Group (JTAG) is an association created by the electronics industry for developing a method of verifying designs and testing printed circuit boards after manufacture. Even if the name is still commonly used, this industry effort has become an Institute of Electrical and Electronics Engineers (IEEE) standard entitled Standard Test Access Port and Boundary-Scan Architecture. Applied in a forensic context, JTAG consists usually of connecting to the standard Test Access Port (TAP) on a device and then instructing the processor to transfer raw data to a connected computer, meaning that JTAG usually requires disassembling the device.
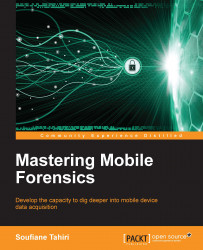
The following are the JTAG TAPs on a disassembled Samsung Galaxy S4 (source http://forensicswiki.org/wiki/JTAG_Samsung_Galaxy_S):

Figure 2
Once the JTAG TAPs are identified, the examiner solders the JTAG connectors to them as shown (source: http://forensicswiki.org/wiki/JTAG_Samsung_Galaxy_S4_(SGH-I337)):
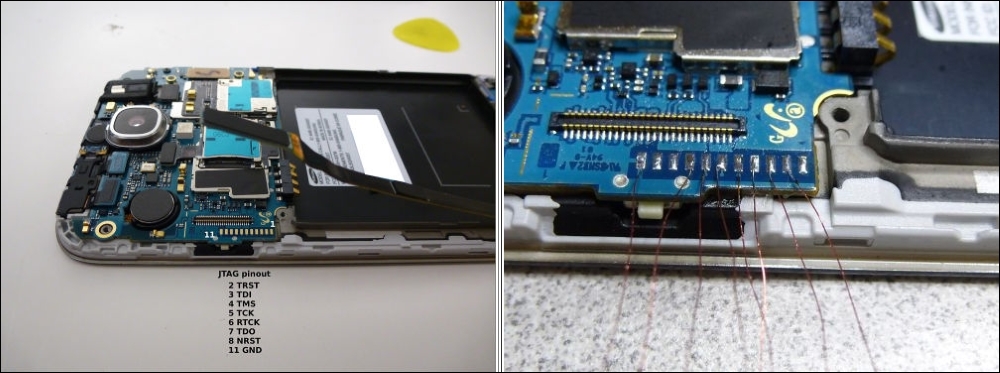
Figure...