MD5 is one of the several well-known cryptographic hash algorithms. Cryptographic hash algorithms compute a compact and unique text representation of input data with arbitrary length, called a digest. This digest can be used to determine if an untrusted input should be trusted by comparing the digest of the untrusted input to a known valid digest of the expected input.
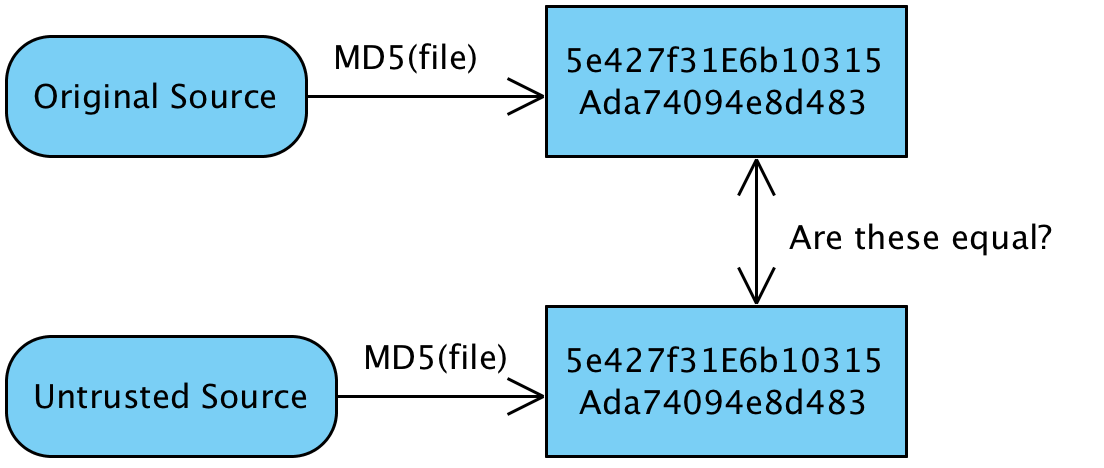
The following diagram illustrates how this works:
For example, many open source software sites allow mirrors to distribute their software to help increase download speeds. However, as a user of the software, we would want to be sure that the software is authentic and doesn't include any viruses. The software distributor will calculate and publish the expected MD5 checksum on their website with their known, good version of the software. Then, we can download the file from any location. Before we install...



