In the previous recipe, we conducted a threat model of a DVR system and rated a threat case that would help with prioritizing vulnerabilities to test. In this recipe, we will go through threat modeling firmware for the same DVR system.
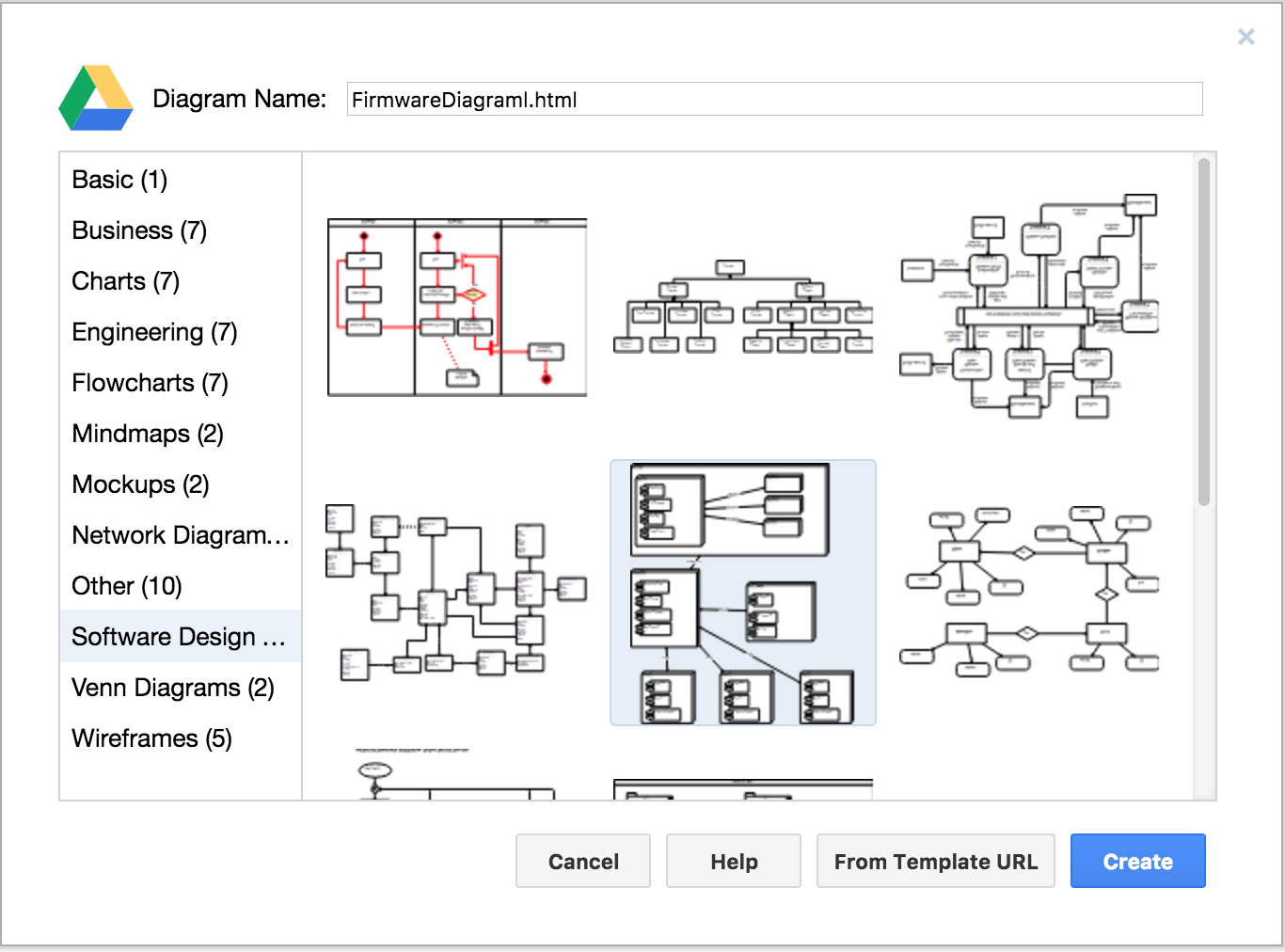
In this exercise, we will use the free https://draw.io online diagram software to help with demonstrating relationships in diagrams within firmware. This tool is a Chrome app and ties to third-party services for storage such as Google Drive or GitHub. We can draw relationships and processes that overlap, which is not possible in the Microsoft tool. Any tool that can effectively draw the architecture with their respective relationships of the target device or software will suffice.
To get started with drawing diagrams, perform the following steps:
- Select
Create New Diagram. - Select
Software Design. - Select the deployment diagram template as shown in the following screenshot:
- Remove all unused diagrams in the template and leave...



