Netdiscover is a great tool for finding potential IP addresses on the network for further examination. It accomplishes this by sending out ARP messages for the given network you specify. By running this tool, you can discover any live hosts on any type of network, wired or wireless. It also attempts to discover the vendor by the MAC address, which can be very helpful in finding vulnerabilities to exploit.
Next is a screenshot with netdiscover tool running in my lab:

This is a tcpdump command of ARP requests that are being sent out by the netdiscover tool to discover these live IP addresses:
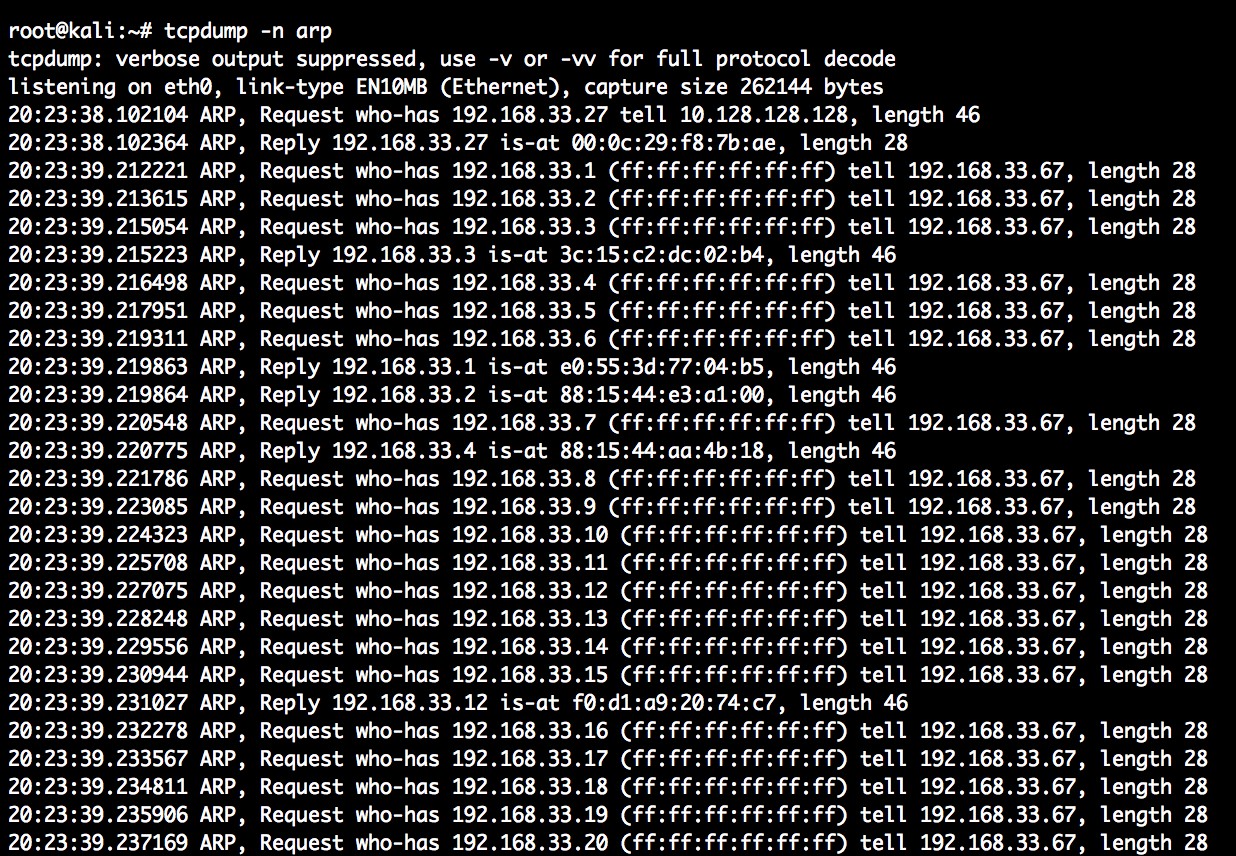
The tcpdump shows how netdiscover does an ARP request for all the hosts in the network range and in this case 192.168.33.0/24. Based on the replies, you can see what is alive currently on the network.