This technique can be used to access the local ports on a machine which are not accessible from outside. Also known as SSH port forwarding or SSH tunneling, this technique allows us to establish an SSH session and then tunnel TCP connections through it.
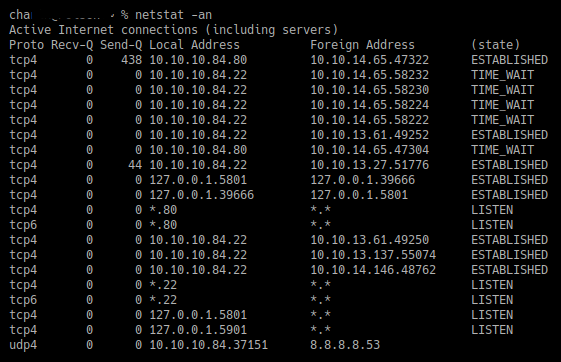
Let's take a look at an example scenario in which we have SSH access to a Linux system. This system has a VNC service running on the machine locally, but is not visible or accessible from outside the network/system. By performing netstat on the machine, we can see that the machine has a VNC service running on port 5901:
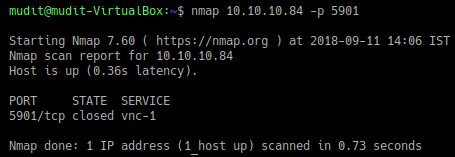
However, by running an nmap scan from outside, we can see that the port is not open:
This is where SSH pivoting comes into use. We can use the following command on our system to forward the port of the remote system onto our system using the SSH tunnel:
ssh -L <local port >:<local...