Servers that are connected to the internet nowadays face a constant daily attacks. As a system administrator, it is recommended you keep a check regularly to ensure that no attacker has been able to get in.
By using different tools, we can keep a check on malware and rootkits, from getting installed on our servers.
In this section, we will see how to install and configure Linux rootkit scanning tools and use as per our requirements:
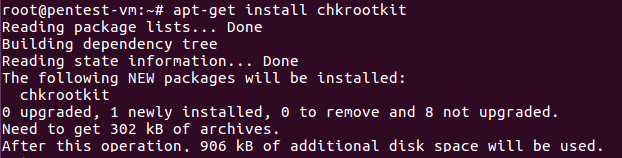
- To begin with, we will install
chkrootkit, a classic rootkit scanner for Linux, as shown here:
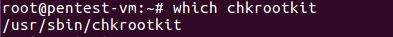
- Once the software has been installed, we can check the path where the software has been installed by running the following command:
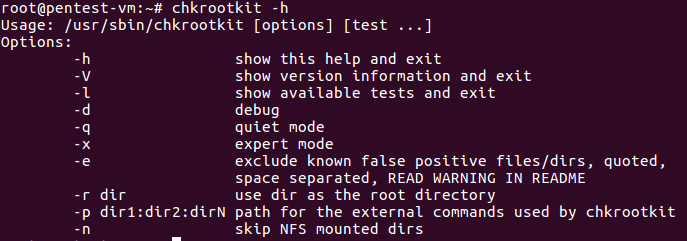
- Next, we check the
Helpmenu to understand the options that can be used to run the tool:
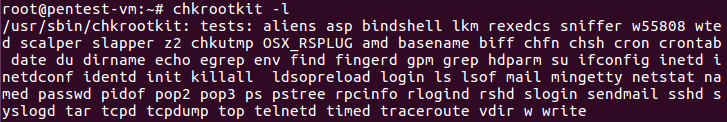
- If we want to see the list of available tests in chkrootkit, we can run the following command: