One of the most widely used command-line packet sniffer or packet analyzer tools for Linux is Tcpdump. It helps to capture or filter TCP/IP packets being transferred or received on a specific interface over the network.
Tcpdump comes pre-installed in most Linux/Unix-based operating systems. If it is not available, we can install it by using the following command:

Once tcpdump has been installed, we can start using it by simply running the command tcpdump:
- When we simply run
tcpdump, it will start capturing all the packets sent or received on any interface.

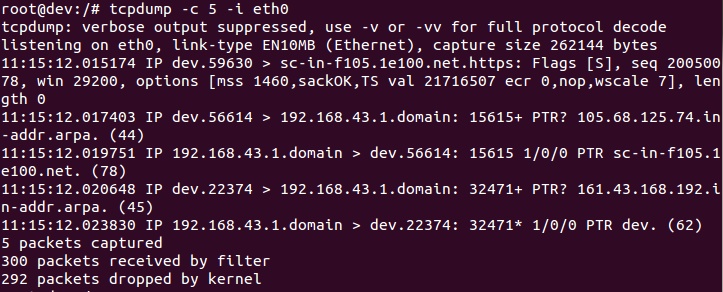
- If we want to capture the packets that are only on a specific interface, we can do the same as shown in the following screenshot:

- The preceding command will capture all the packets received on the defined interface, until manually stopped. If we wish to capture a specific count of packets, we can do so by using the
-coption, as follows:
- To display the captured packets...



