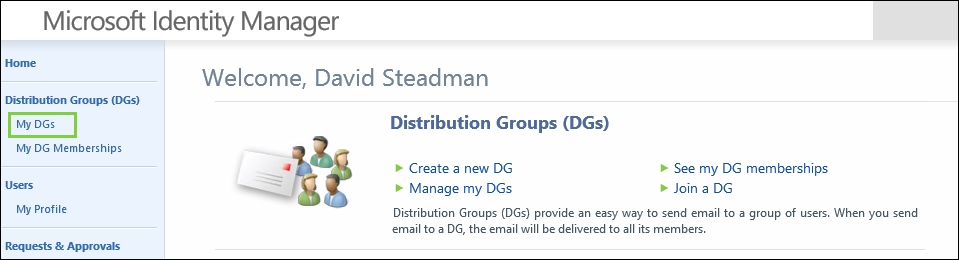
After allowing employees to create distribution groups earlier, we can now see what they would look like from a user's perspective.
There are different parts and steps involved in managing distribution groups. Let's start with how John creates a new distribution list:
David (who is an employee) logs on to the MIM portal, and selects My DGs. So far, it is empty. He would like to create one, so he clicks on New:
He gives his new group a display name, Hunters, and an e-mail alias, Hunters. A good description is always useful so that others can decide whether this is a group they would like to join:

David will automatically be added as the first member, and he...