As stated in the introduction, point-to-point networks are an excellent choice when connecting a small number of endpoints. In this example, we will show how to connect three sites together using point-to-point tunnels. It will also show how quickly the configuration of such a setup can become very complex.
Consider the following network layout:
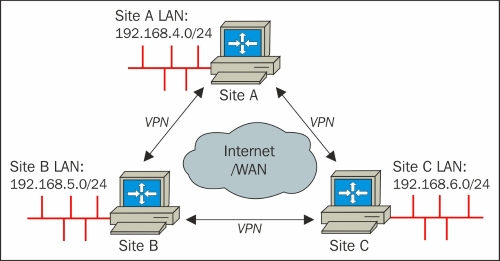
We will create three tunnels between the sites and set up redundant routes. That way, if one of the tunnels goes down, all the sites will remain visible to each other. However, this is at the cost of a performance penalty. Let's assume that the link between site A and site B goes down. The backup route goes from site A to site C to site B, so now traffic from site A to site B has to make an extra hop.
First, we create three secret keys:
$ openvpn –-genkey –-secret AtoB.key $ openvpn –-genkey –-secret AtoC.key $ openvpn –-genkey –-secret BtoC.key
Then, we transfer these keys to all endpoints over a secure channel (for example, using...