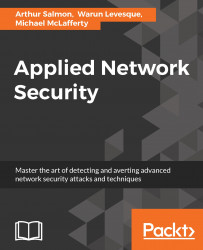
Another powerful tool found within the Veil Framework is called Veil-Pillage. What is Veil-Pillage and how does it work? Veil-Pillage is a post-exploitation framework consisting of multiple modules. It was released at the 2014 Defcon and has since attracted lots of praise for its effectiveness. In the following screenshot you can see some of the modules found within Veil-Pillage:
Veil-Pillage has similar commands and interface are similar to those in the Metasploit msfconsole. This makes it easier to learn.
To bring up Veil-Evasion, follow these steps:
- Type ls and then cd Veil-Evasion.
- Next type ls and then type ./Veil-Evasion.py. In order for Veil-Evasion to start you must change directories to the Veil-Evasion folder and execute the tool from there:

- After starting Veil-Evasion you will see a menu screen, which will give you a number of options. From these options, we will select list:
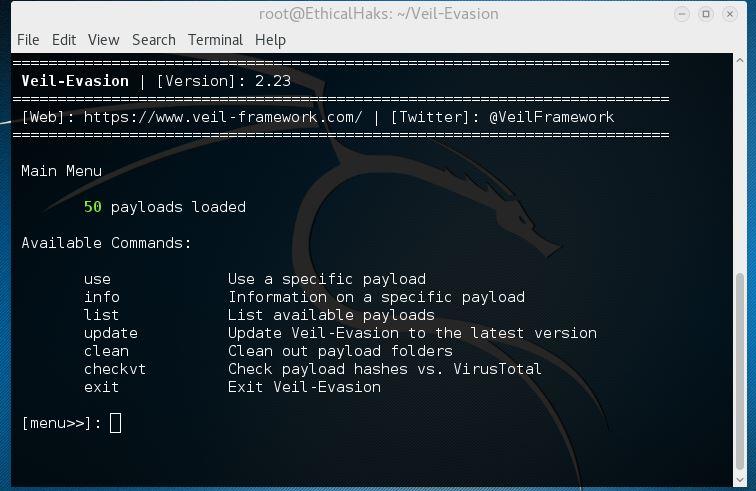
The list...