Vega is a Web vulnerability scanner made by the Canadian company Subgraph and distributed as an Open Source tool. Besides being a scanner, it can be used as an interception proxy and perform, scans as we browse the target site.
We will use Vega to discover Web vulnerabilities in this recipe.
Open Vega by selecting it from the Applications menu by navigating Applications | Kali Linux | Web Applications | Web Vulnerability Scanners | vega, or from the terminal:
vega-
Click on the Start New Scan button (
 ).
).
A new dialog will pop up. In a box labeled Enter a base URI for scan: we enter
http://192.168.56.102/WackoPickoto scan that application:
Click Next. Here we can select what modules to run over the application. Let's leave them as default.

Click Finish to start the scan.
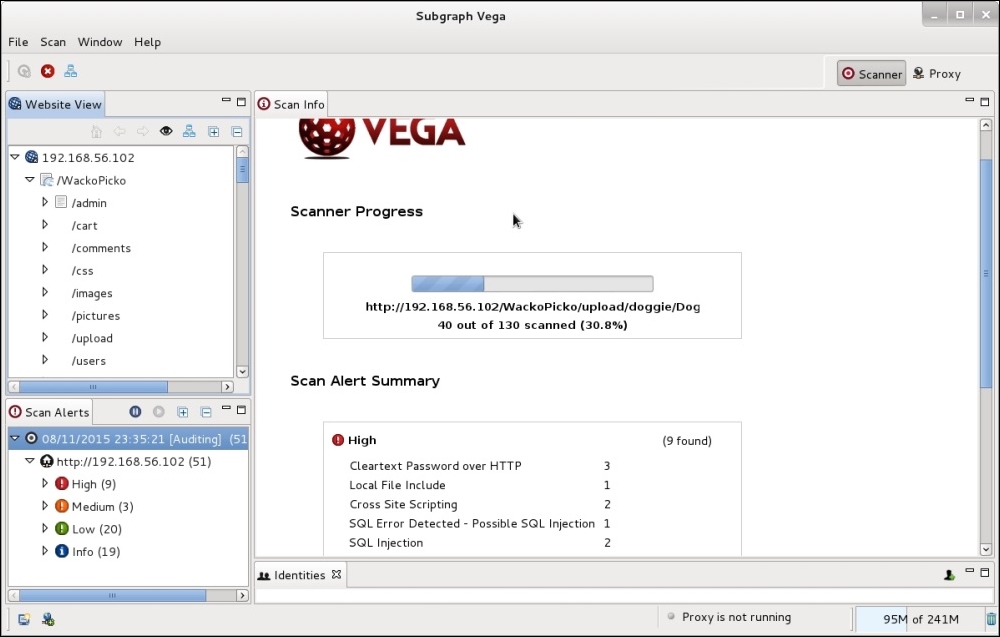
When the scan is finished, we can check the results by navigating the Scan Alerts tree in the left. The vulnerability details will be shown in the right panel, as shown: