What is vRealize Configuration Manager (VCM) and what it can do for you?
vRealize Configuration Manager is a complete configuration management solution provided by VMware. This is a part of the vRealize Operations suite along with vRealize Operations Manager, vRealize Hyperic, and vRealize Infrastructure Navigator, to name a few. Being a part of the suite, VCM is responsible for compliance and patch management, these being its core functionalities.
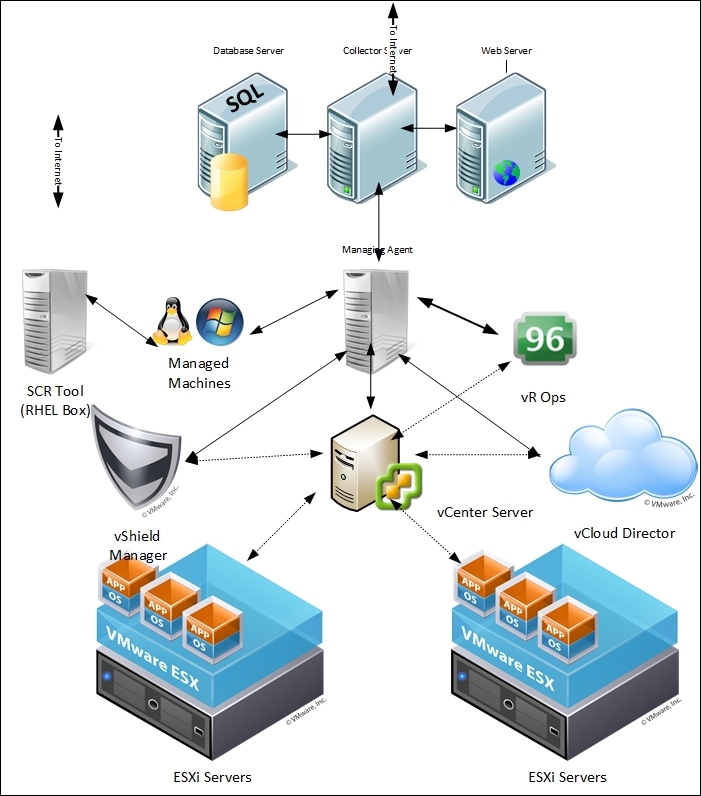
VCM is a tool that collects data automatically from managed machines, which may be running Windows or Unix, and virtualization tools such as vCenter, vShield, and vCloud Director, and based on that data, VCM can perform compliance checks and help you manage your virtual machines from the console.
VCM can perform the patching of managed machines, which may either be physical or virtual, and Windows and many flavors of Unix/Linux are supported, such as Red Hat Enterprise Linux (RHEL), SUSE, CentOS, and Mac OS. To patch these operating systems, we need a RHEL server acting as a patch repository. For non-windows servers, this RHEL patch repository downloads the patches, and all the managed machines can come and download them over HTTP, HTTPS, FTP, or NFS. VCM can patch all the supported versions of Windows.
You can download various compliance packs created by VMware and others. Just download and import them, and they will be ready for use with your managed machines. The packages include but are not limited to security best practices developed by the Defense Information Systems Agency (DISA), the National Institute of Standards and Technology (NIST), the Center for Internet Security (CIS); regulatory mandates such as Sarbanes-Oxley (SOX), the Payment Card Industry (PCI) standard, the Health Insurance Portability and Accountability Act (HIPAA), and the Federal Information Security Management Act (FISMA); and hardening guidelines from VMware and Microsoft.
You not only can check the compliance of your infrastructure but also enforce it to enhance your compliance score. Enforcing compliance means VCM can make necessary changes to the server to make it compliant.
This does not limit you from creating your own rules and compliance templates; you can either create a completely new rule or combine rules from various rulesets provided by VMware.
VCM can be used to install an operating system on bare metal, or you can deploy a virtual machine. You can use VCM to deploy applications on managed machines, which is limited to Windows. With features such as VCM Remote Client, you can manage communication and management mechanisms for mobile Windows machines as they connect to and disconnect from the network.
With the vRealize Operations (vROps) Manager Management Pack, you can push the compliance score of managed virtual machines to the vROps console. vROps is a monitoring solution from VMware used to monitor virtual infrastructure; pushing the compliance score to the console gives us the view of the infrastructure under one console. Also, if required, an alert can be configured if the score goes beyond a certain limit.
Along with all this, we can use VCM to manage Active Directory. VCM for Active Directory collects Active Directory objects across domains and forests and displays them through a single console. The information is consolidated and organized under the Active Directory slider, allowing you to view your Active Directory structure, troubleshoot issues, detect changes, and ensure compliance.
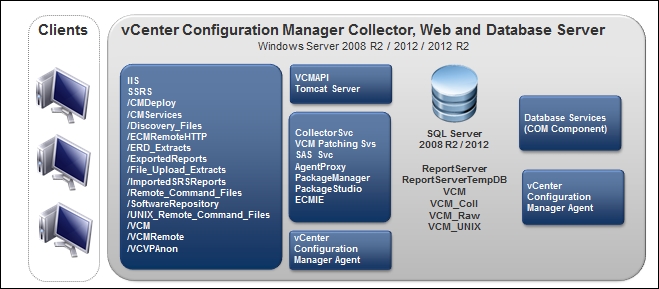
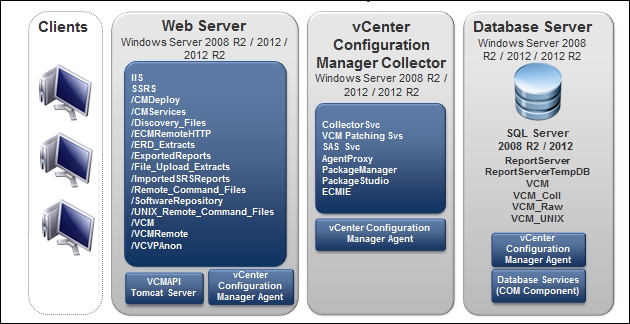
VCM is an application composed of multiple components, as described in the following figure:
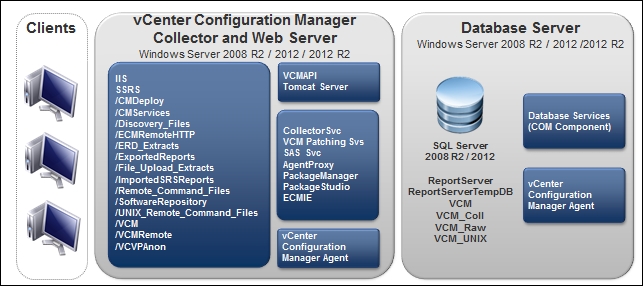
The database server contains the VCM, VCM_Coll, VCM_Raw, and VCM_UNIX databases. Using a shared SQL Server instance is supported by VCM. However, VCM makes heavy use of SQL Server for query and transaction processing. You must ensure that you have or can add enough capacity to a shared SQL Server instance so that VCM and any other databases on the shared server do not experience poor performance.
VCM operates with the Standard, Enterprise, or Datacenter editions of SQL Server. You must install the 64-bit SQL Server 2008 R2, 2012, or 2014 versions on the database server used by VCM.
The SQL Server license must include SQL Server Reporting Services (SSRS), which is used by VCM for the reporting feature.
The VCM Collector is a standalone application that can run even when no other VCM components are active. This is particularly useful in the case of scheduled collections, because it means the VCM Portal does not have to be up and running. The Collector has all the necessary information and capabilities to perform the requested functions. You can stop the Collector and still look at data as the UI does not interact directly with the collector service; instead, it communicates with various executables that are installed on the same machine as the Collector.
Windows patches will be hosted on the VCM Collector as per the default configuration. Linux patches will be handled by the Standby Continuous Replication (SCR) server. We will have a look at Linux patching in Chapter 3 , Linux Patching.
Supported operating systems for installing the VCM Collector are Windows Server 2008 R2, 2012, or 2012 R2. The VCM Collector must be installed on a AD domain member.
We will discuss the installation of the VCM Collector server in multiple recipes in this chapter.
The web server contains web applications such as IIS and SSRS, other services, and VCM software components. Before you install VCM, you must configure the web server. The Windows machine that hosts the web components must be running Internet Information Services (IIS) 7.5. Supported operating systems to install the web server to are Windows Server 2008 R2, 2012, or 2012 R2.
We will discuss the installation and configuration of the web server in the Preparing our VCM deployment - installing and configuring IIS recipe.
We need to install an agent to manage the machines through VCM. In the case of vCenter Server, vCloud Director, and vCloud Networking and Security Manager, VCM uses an intermediary managing agent for data collection. This intermediary collects data through the use of the vSphere VIMAPI, vCloud REST API, and vCloud Networking and Security Manager REST API, and it then passes it to VCM Server.
We need to install VCM agent 5.5 or higher on the system designated as being the managing agent. However, after the agent deployment, there is an additional step. Mutual two-way trust must be established with the system designated as the managing agent before the collection of any vCenter, vCloud Networking and Security, or vCloud Director data can be done.
The vCenter collection process via the managing agent is serial and very CPU intensive. For this reason, a separate managing agent is recommended for virtual infrastructures. If the number of vCenter or vCloud Server instances increases, the number of managing agents can be horizontally scaled.
We will see this in action in the Chapter 2, Configuring VCM to Manage Your Infrastructure, in the Configuring a managing agent machine for virtual environment management recipe.
To ensure that all patch dependencies are met when VCM deploys the patches, the SCR Tool downloads all of the necessary patches (except for patches that have been superseded by newer patches). VCM patching handles all the dependencies when the patches are deployed. If the patch was available when the SCR Tool was installed and configured, it would have been downloaded. If the patch was not available when the SCR Tool was last synchronized, it would not have been downloaded and hence not available for distribution to managed machines. If the patch is still available from the OS vendor, it will be available for download using the SCR Tool patch-replication process. The SCR server does not share or sync the details of the patches downloaded by it; VCM gets the details of the released patches from http://www.vmware.com/ . So, we need to make sure is fully synced with vendors such as RHEL or SUSE and has all the patches downloaded in the repository.
The SCR Tool is not used to run patch assessments or deployments. It also does not assess the machine configuration or the downloaded patch content that is used for patch deployment. That job is done by the VCM server.
The SCR Tool downloads the patch signature files and OS vendor patch content from the content distribution network (CDN) and downloads subscription-only content from the OS vendor's content web sites. We will look at this in more detail in Chapter 3 , Linux Patching.
Depending upon the size of the infrastructure you manage, VCM can be deployed in multiple ways.
If you plan to install VCM on two or three tiers, check out this link for how to size your hardware environment: http://kb.vmware.com/kb/2033894 .
A single-tier installation can be used by organizations smaller than 2,000 managed servers and POC/pilot engagements.
All the components, such as the VCM Database server, web server, and the VCM Collector, are installed on the same server, like this:
A two-tier installation can be used by organizations where the number of managed servers is between 2,000 and 5,000.
In this deployment, we have the application server (Collector) and IIS on one machine, SQL Server instance on the other machine, and SSRS on either system, as shown here:
A three-tier installation can be used by organizations with more than 5,000 servers. It is constructed in this manner:
The application server (Collector), IIS, and SQL Server instance are on separate machines
SSRS can be either on the IIS or the SQL Server system
This figure depicts a three-tier installation:
Every software application we install has its own requirements for successful installation and functioning. VCM is no different. In this section, we will discuss the hardware and software requirements for getting VCM deployed.
We need the following software to install VCM:
|
Software component |
Versions supported |
|
Operating system for VCM Web, Collector, and Database server |
Windows Server 2008 R2, Windows Server 2012, or Windows Server 2012 R2 |
|
SQL version |
SQL Server 2008 R2, 2012, or 2014 Standard, Enterprise, or Datacenter Edition (64-bit) |
|
SSRS version |
SQL Server 2008 R2, 2012, or 2014 Reporting Services |
|
OS for SCR* |
RHEL 7.x |
(*SCR: software content repository. It is used to download and store patches for non-Windows operating systems)
Hosting the VCM has some hardware requirements as well, which are provided in the following tables:
Minimum hardware requirements to support 1-1,000 managed machines:
|
Single Tier |
2-Tier
Database |
2-Tier
Web/Collector |
3-Tier
Database |
3-Tier
Web |
3-Tier
Collector | |
|
RAM |
8 GB |
8 GB |
4 GB |
8 GB |
4 GB |
4 GB |
|
Processor |
Dual Xeon or single dual-core 2 GHz |
Dual Xeon or single dual-core 2 GHz |
Dual Xeon or single dual-core 2 GHz |
Dual Xeon or single dual-core 2 GHz |
Single 2-GHz processor |
Single 2-GHz processor |
Minimum hardware requirements to support 1,001-2,000 managed machines:
|
Single Tier |
2-Tier
Database |
2-Tier
Web/Collector |
3-Tier
Database |
3-Tier
Web |
3-Tier
Collector | |
|
RAM |
12 GB |
12 GB |
4 GB |
12 GB |
4 GB |
4 GB |
|
Processor |
Quad Xeon or two dual-core 2 GHz |
Quad Xeon or two dual-core 2 GHz |
Quad Xeon or two dual-core 2 GHz |
Quad Xeon or two dual-core 2 GHz |
Single 2-GHz processor |
Dual Xeon or single dual-core 2 GHz |
Minimum hardware requirements to support 2,001-5,000 managed machines:
|
Single Tier |
2-Tier
Database |
2-Tier
Web/Collector |
3-Tier
Database |
3-Tier
Web |
3-Tier
Collector | |
|
RAM |
16 GB |
16 GB |
8 GB |
16 GB |
4 GB |
8 GB |
|
Processor |
Eight-way Xeon or four dual-core 2 GHz |
Eight-way Xeon or four dual-core 2 GHz |
Dual Xeon or single dual-core 2 GHz |
Eight-way Xeon or four dual-core 2 GHz |
Single 2-GHz processor |
Dual Xeon or single dual-core 2 GHz |
Let's look at the list of accounts and the privileges required for VCM to work properly.
You can reuse an account for more than one function, but dedicated accounts might be useful for troubleshooting and tracking.
The Collector, VCM Remote, Tomcat, and vSphere Client VCM plug-ins can be used from the same account. If you reuse one account, apply the permissions shown for the Collector service account.
|
Role |
Permissions |
Description |
|
VCM Administrator |
(During installation only) Local admin access on the VCM Collector and Web server.
(During installation only) System admin access to the VCM SQL Server instance on the database server.
This must be an interactive account and separate from the other accounts in this table. |
The VCM Administrator account is the login account used when installing VCM and possibly post installation for the administration and maintenance of VCM. |
|
VCM Collector Service |
Local admin access on the VCM Collector and Web servers.
This is not a domain administrator or interactive user account. |
The Collector service account is the account under which the VCM Collector, VCM Database, and VCM Patch Management services run. During installation, VCM configures the Collector service account with DBO and bulk insert rights in SQL Server for the VCM databases. |
|
VCM Remote Service |
Local admin access on the VCM Web server.
This is not a domain administrator or interactive user account. |
The VCM Remote service account is used by the VCM Remote client for anonymous access to the VCM Remote virtual directory on the Web server. |
|
VCM Tomcat Service |
Local admin access on the VCM Database server.
Public access on VCM databases.
This is not an interactive user account. |
The Tomcat service account serves as the VCM application programming interface for SQL login to the E12VCM Database server. |
|
vSphere Client VCM Plug-in Service |
Local admin on the VCM Web server.
This is not an interactive user account. |
The vSphere Client VCM Plug-In (VCVP) account provides vSphere access over HTTP to VCM managed machines.
The VCM Advanced Installation option prompts for credentials for the VCVP account. Typical Installation does not. |
|
VCM Default Network Authority |
Local admin access on Windows machines that VCM collects from using the DCOM agent.
Depending on the enterprise size and for convenience, a separate, domain administrator account with rights on the Windows machines.
This is not an interactive user account. |
The network authority account is for data collection from DCOM Windows machines. |
Tip
IMPORTANT: Never use the service accounts for logging in to the VCM Console or for any other purpose. Logging in to VCM using a service account can lead to unexpected or inconsistent behavior. Services that use the same account as a logged-in user might modify the logged-in user's current role or machine group or log the user out of the system.
If for some reason you don't get a local admin account to be used as the NAA, you need at least the privileges mentioned in the following table. For VCM to make changes on licensed machines, such as rebooting and managing audit settings, the account used to interact with the VCM agent needs the following permissions and rights on each licensed machine:
|
Action |
Required user right |
|
Emergency repair disk |
Back up files and directories |
|
NTFS permissions |
Manage auditing and security logs |
|
Reboot |
Shut down the system, force shutdown from a remote system |
|
Services change |
Shut down the system |
|
Share permissions |
Manage auditing and security logs |
To check or set the appropriate rights on each machine, you can use either of these:
Local security policy: Security Settings | Local Policies | User Rights Assignment
Group Policy plugin: Local Computer Policy | Computer Configuration | Windows Settings | Security Settings | Local Policies | User Rights Assignment
There are four databases created by VCM; there is a list of them along with their purpose in the following table. The databases are created when we deploy VCM using the installer.
|
Database name |
Minimum size |
Purpose |
|
|
3 GB |
This contains configuration data for the VCM application itself, collected data from Window systems and virtual infrastructure, change details from all systems, and results of patch and compliance assessments. The base name |
|
|
1 GB |
This provides operational state information for the Collector service and is mainly used to track details of running jobs and the last contact state of managed client systems. |
|
|
1 GB |
This contains the collected managed machine data gathered from any Linux, Unix, or Mac agents in the environment. |
|
|
1 GB |
To improve performance, this database temporarily holds collection data before it is transformed into the |
The list of OSes supported by VCM is as per the following table, but this is not a comprehensive list.
You can take a look at the Hardware and Operating System Requirements for VCM Managed Machines chapter of the VMware vRealize Configuration Manager Installation Guide ( http://www.vmware.com/pdf/vrealize-configuration-manager-58-installation-guide.pdf ) for the complete list.
|
Supported operating system |
Supported hardware platform |
|
Microsoft Windows Server 2003 SP2 |
x86 and x64 |
|
Microsoft Windows Server 2008 R2 Enterprise Gold |
x64 |
|
Microsoft Windows 7 Enterprise Gold |
x86 and x64 |
|
Microsoft Windows 8.1 Enterprise |
x86 and x64 |
|
Microsoft Windows Server 2012 R2 Datacenter |
x64 |
|
Red Hat Enterprise Linux 5.0-5.11, 6.0-6.5, and 7.0
(x64) Server, Desktop with Workstation, and Advanced Platform |
x86 and x64 |
|
SUSE Linux Enterprise Server (SLES) 10.0-10.2 (up to agent version 5.5.0 only)
SUSE Linux Enterprise Server (SLES) 10.3-10.4, 11.0-11.3, and 12 |
x86 and x64 |
|
Windows 10 |
x86 and x64 |
The following table shows the port and protocol requirements for proper functioning in the environment:
|
Source |
Target |
Port and protocol |
Description |
|
Managing agent |
vCloud Management vCenter |
HTTPS: 443 |
The web service connection to the vCenter API.
Valid credentials and certificate thumbprint are required. |
|
Managing agent |
vCloud vCenter |
HTTPS: 443 |
The web service connection to the vCenter API.
Valid credentials and certificate thumbprint are required. |
|
VCM Collector |
VCM Database Server |
SQL: 1433 |
Windows authenticated connection. |
|
VCM Collector |
VCM Database Server |
DCOM: 135 |
DCOM is required between the Collector and the DB Server in a two-tier configuration so that the DB server can call back to the Collector at the end of various jobs. |
|
VCM Collector |
VCM Database Server |
SMB: TCP ports 139 and 445 |
VCM creates a share to the DB server during installation. |
|
VCM Collector |
VCM Database Server |
HTTP: 80 |
An SSRS connection from VCM Server to the DB SSRS instance. |
|
VCM Collector |
VCM Database Server |
ICMP |
Login details are not sent to the agent.
Mutual authentication is used and the agent runs under LocalSystem. Data is pulled back to the Collector over a new TLS session. |
|
VCM Collector |
Agent |
HTTP: 26542 |
Login details are not sent to the agent.
Mutual authentication is used and the agent runs under LocalSystem. Data is pulled back to the Collector over a new TLS session. |
|
VCM Collector |
Agent |
ICMP |
Login details are not sent to the agent.
Mutual authentication is used and the agent runs under LocalSystem. Data is pulled back to the Collector over a new TLS session. |
|
VCM Collector |
Agent |
SMB: TCP ports 139 and 445 |
This is a mapped driver for Windows patch downloads. |
|
Agent software |
RedHat Patch Server |
HTTPS: 443/80 |
This depends on how you have configured Apache, which will be used to download patches from the patch repository. |
vRealize Operations is available with two license models:
Per processor with unlimited VMs: For virtual environments with high consolidation ratios, vRealize Operations is available per processor as a part of VMware vRealize Suite, VMware vCloud Suite, and VMware vSphere with Operations Management.
Per virtual machine or physical server: For virtual environments with low consolidation ratios, vRealize Operations is also available à la carte in 25 VM or OS instance license packs.
The new release, VCM 5.8.2, supports Hybrid Cloud Suite license keys, as VCM will not be part of vCloud Suite anymore. This keeps changing; you can contact VMware for current pricing details or check out more details here: https://www.vmware.com/products/vrealize-operations/pricing .