Understanding the basics of end user functionality
Before we can change any settings for end users to optimize their experience, we must understand what their interface looks like and what we can change. As mentioned before, when an end user logs in to the dashboard, they see all available applications. By default, they have a tab called Work, where they can add their own tabs and organize their applications.
On the end user dashboard, users can modify how apps are shown, add their own applications, and manage any credentials within the apps that are set up as Secure Web Authentication (SWA) applications.
Let’s go over the different sections on the dashboard:
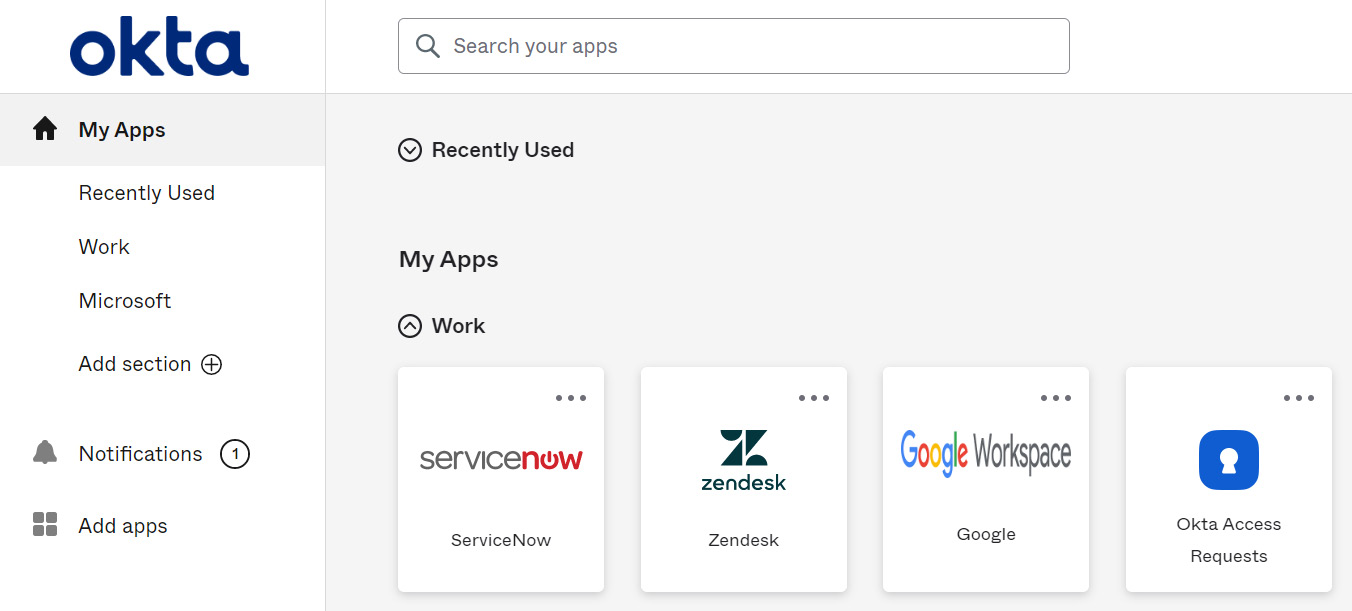
Figure 6.1 – The end user dashboard
The left column is where users can find the different sections they have and quick links to the App catalog (found under the Add apps option) and Notifications sections. In the search bar at the top, users can easily search for an application...