In most cases, we don't need to call another function present in the program itself. Instead, we need to place shellcode in our attack vector, which will perform any malicious activity specified by us in the shellcode. However, in most devices based on the ARM platform, the region in memory is non-executable, which prevents us from placing the shellcode and executing it.
So, an attacker has to rely on what is known as return-oriented programming (ROP), which is simply chaining up pieces of instructions from different parts of memory, which will finally execute our shellcode. These pieces are also known as ROP gadgets. In order to chain the ROP gadgets, we need to find the gadgets that have an instruction at the end, which will allow us to jump to another location.
For example, if we disassemble seed48() while executing the program, we will notice the following output:
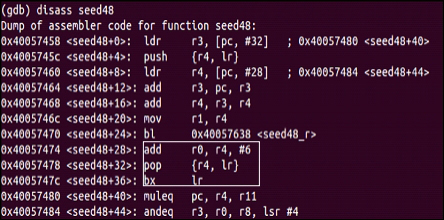
If we look at the disassembly, we will notice that it contains an ADD instruction followed by a...