Preparing to install Kali Linux onto a computer system is similar to other OS you may have encountered, starting with ensuring you have the right system requirements.
Installing Kali Linux
Getting ready
To get things started, let's look at the minimum hardware requirements that you will need to have in place to even get the product to install:
- Minimum of 10 GB hard drive space for the Kali OS
- For i386 and amd64 systems 512 MB of RAM
- CD/DVD drive or USB boot support
- An active internet connection is desirable
Again, keep in mind what is listed here represents the bare bones minimum and you will want to exceed these by as wide a margin as possible to ensure decent to excellent performance. Personally, I would recommend having at least 4 GB of RAM, if not more (I personally have 8 GB or 16 GB in the systems I use respectively, but I have used 4 GB of memory in the past and been fine).
How to do it...
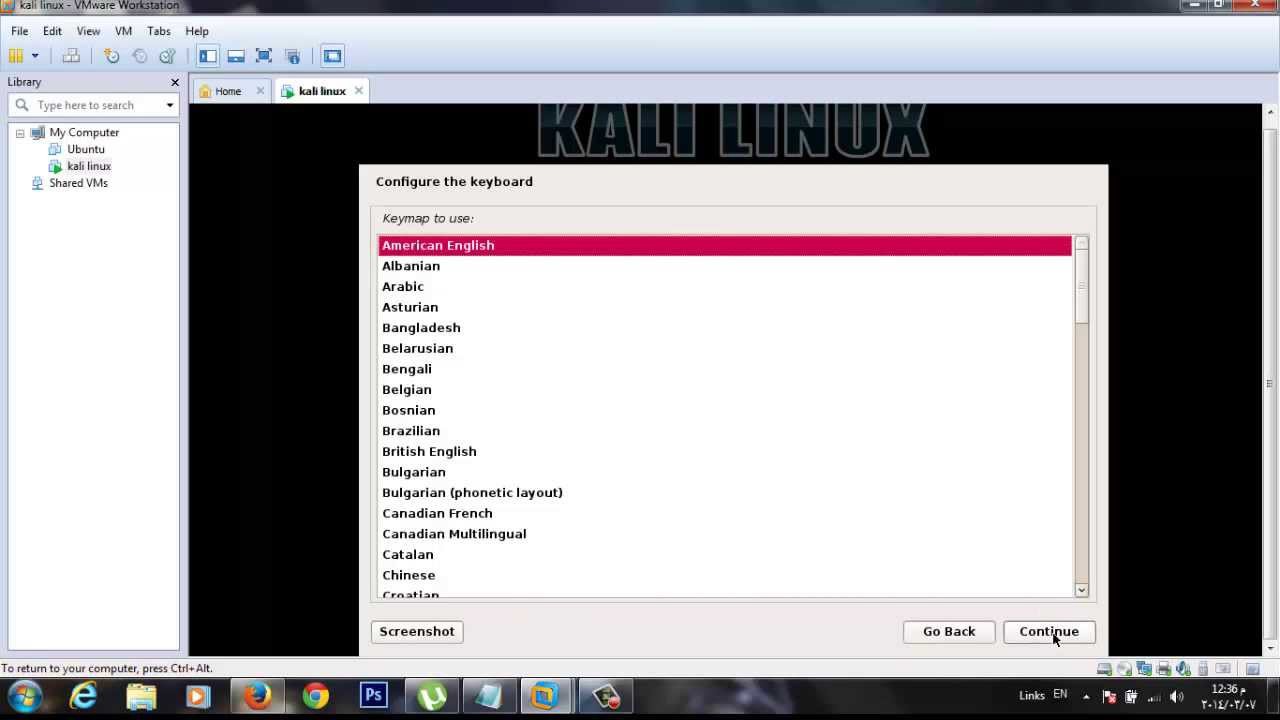
Once you have confirmed or upgraded your system's hardware as needed you now need to choose how you will install Kali. Kali offers several different ways to install and run the product each having its own benefits, but also with their own drawbacks as well. However, for this book we will assume one of two options, these being physical installation on a PC and within a virtual environment.
Virtualized versus physical
The question of using virtualization instead of installing directly on a system is one issue that you should consider. Virtualization is a common option that has been employed for many years by organizations large and small, with many organizations using it liberally for various needs. For many the driving force for moving to virtualization can be many factors, including consolidation of systems, saving power, optimizing hardware usage, isolation of applications and systems, ease of management as well as testing just to name a few.
However, for a penetration tester, the use of virtualization tends to be a bit different.
One of the motives on the pentester side is being able to run your testing environment in different configurations on top of a host. For example, running Microsoft Windows as a host with one or more Kali environments running as guests in a virtualized environment on top of the system allows for consolidation, along with the ability to have specialized configurations as needed.
Another reason for the move to virtualization is to make use of what is known as isolation or sandboxing. Basically, this means that the guest system is separated from the host system allowing both access off of system to the network and internet without letting the two potentially interfere with one another. This would be vital in situations when the tools and skills being used in the guest may have the ability to harm or compromise the host or other systems.
Of course, you don't get something for nothing and not everything is ideal in every situation and virtualization is not any different. One area which can prove problematic is in relation to hardware support. In some cases, physical devices may not be able to function in the way you need them to function due to the virtualization technology. One example is wireless networking and Bluetooth; these technologies may require that Kali is run directly on the hardware instead of within a virtual environment. While this limitation is not common it can be frustrating. Of course, I would be remiss if I didn't mention that there are workarounds and it is possible to get some hardware options to work in a virtualized environment that wouldn't otherwise, but these workarounds can be very complex and specialized, and are beyond the scope of this work.
Pre-installation checklist
Much like many operating systems which are available, Kali has some unique and specific points that need to be considered in order to make the installation proceed properly. Fortunately, Kali keeps its installation requirements fairly simple, but there are definitely things that could impact your experience and make Kali operate in a less than stellar manner.
To make sure we get the optimal installation and performance, here is an example of a checklist of items to consider:
- Will you install Kali to the hard drive or will you run it from removable media?
- How much memory is currently on the system? More memory makes for a better experience and better performing Kali system. On my own personal system, I run with 8 GB and Kali runs beautifully. If you run Kali off of something other than the hard drive, more memory may allow for better performance as more of Kali can be kept in memory.
- What applications will you be running? If you will be installing additional applications into Kali, you may need to adjust your configuration to account for their inclusion. Some utilities require special hardware (such as wireless devices) to be present in order to function properly. If you rely on these functions or will use them in the future, ensure that all your hardware is compatible or can be upgraded.
- What type of hard drive do you have? I have run Kali off of both traditional drives and SSD and, of the two, SSDs run much better and make for a more satisfying experience and performance.
- Software support for your favorite applications and devices is very broad with Kali and has only increased over time. Applications have been included with Kali which cover many uses and situations you may run into, but you can add to this as needed.
Choosing an installation option
After we have assessed our system's suitability for an installation of Kali we now need to consider how it will be installed. It is likely that more than a fair share of you reading this book will have extensive experience in a Windows environment and, as such, you will have almost always installed an OS to a hard drive directly. However, as we just learned Kali, offers additional installation options. We now need to make a determination of which path we are going to take in regards to installation location.
Let's look at the main options and what makes each a good choice or bad choice:
- Installing to a flash drive without persistence: This is a suitable installation method if you wish to use Kali to perform forensics, as it will not alter the host and therefore not affect potential evidence on the system. It is also a very suitable installation method if you wish to have Kali assist you with network or host troubleshooting. It may also be ideal if you want to have a portable environment that you can run on any system without having to worry about changes to the host or to the flash drive itself.
- Installing to a flash drive with persistence: This installation method is suitable for situations where you want to be able to carry Kali with you for troubleshooting, forensics or to have a portable pentesting kit, but you wish to be able to save files and make changes to the system without losing those changes every time you shut the system down.
- Installing to a hard drive: This is extremely popular and useful because it offers the best performance, since the files don't need to be loaded into memory each boot. This installation also offers the ability to save files and make changes without losing either upon reboot. It is ideal if you want to have a system that retains changes, especially if you tend to tweak a system to your own needs.
- Installing as a virtualized environment: This option is just like installing to a hard drive except the OS is being installed into a virtualized environment that allows changes to the Kali guest.
- Running from a CD or DVD: I've included this here because this is another option similar to installing Kali to a non-persistent flash drive. This tends to be slower in operation than any other method covered here.
If very specific hardware, such as high-powered graphics cards, will be used for cracking passwords, it is recommended that the installation of Kali Linux be installed on a desktop computer. If there is a need to carry the operating system from customer site to customer site, or there is a desire to test wireless devices, a laptop is recommended. The installation of the operating system is the same for laptop and desktop computers.
My choice of laptop was based on a couple main issues namely hardware support and power. By choosing a slightly older system I didn't have to worry about Kali supporting the hardware, nor did I have to worry about having to look for solutions to make the system work, it just did. In regards to power, I am referring to the fact that Linux traditionally doesn't need the most powerful hardware to get good performance. In fact, Linux has traditionally been known to run on older hardware without the problems other operating systems would experience. However, I made sure I didn't go back so far that I would be constrained with the tools I need to use. I have found that hardware that has been manufactured in the last five years or less will generally be OK to run Kali in most cases.
Hard drive selection
One of the areas you don't want to cut corners on when choosing a system for Kali is that of the hard drive. It is usually a good idea to get a drive that has at least 150 GB of space, but you should consider drives larger than this if possible, as you will undoubtedly install other tools that aren't included in Kali (not to mention the data you generate will take up space as well).
Keep in mind that, as a penetration tester, you will be not just asked, but required to keep your findings confidential and, for many tests, this means wiping the hard drive to be safe. While it is possible to clean an installed OS so it is returned to its base or original unaltered state, you still may want to wipe the drive. The suggestion would be to set up the system the way you desire then image it so you can effectively wipe a drive then restore your original image at will. Always keep in mind that losing control of or leaking information is something that will not only upset your client, but open you up to lawsuits, loss of reputation, loss of career, and bad karma. Basically, take the proper precautions with the data you have gathered both during and after a test.
First, the use of an SSD drive will typically result in the reduction of battery drain on a system to some degree. This reduction in battery drain results in longer mobile use when you can't plug into a wall.
Second, SSD drives are faster than traditional hard drives by a substantial amount. SSD drives result in faster read and write times than a traditional hard drive. Being able to retrieve and manipulate data faster is a tremendous benefit for a penetration tester (or anyone for that matter).
Lastly, SSD drives can take a lot more of a beating than older traditional drives. The lack of a spinning disk inside the computer means that moving and transporting the drive plus system is a lot less likely to result in drive failure.
These are the things I considered when moving to a solid-state and I don't feel like I made a bad choice.
Network cards and wireless
Something you need to consider with Kali is how you will be connecting to networks as well as what types of tests you may be performing. Namely, what we are considering in this section is your choice of network interface, that is, wired or wireless. Wireless is a common inclusion on just about any class of device you will run into today (or those made in the last 10 years). On the other hand, wired network connections on devices have become less common with many notebooks and laptops dropping them altogether.
In the case of wireless networking, you may find that many of the wireless network cards which are either included in your device or are added via other means such as USB will work with Kali without issue or can be corrected by acquiring the right drivers from the manufacturer. The following figure shows one example of a popular USB wireless network adapter:

The other form of wireless you may perform some testing with is Bluetooth, in which case you probably will need to acquire an additional adapter for this purpose. The reason for purchasing another adapter is that fact that Bluetooth, by default, only extends out to 30 feet or 10 meters in range. If you need greater range to enable the scanning of a larger area you can acquire an Industrial Bluetooth adapter which extends scanning range to 1000' or more.