By default, for every SSL connection, when an Android app connects to a server, it validates the server's certificate and checks whether it has a valid trusted root certificate and also matches the reverse DNS (hostname). By defeating this feature, one can perform an MitM attack.
Since we have all the setup required to perform an MitM attack from Chapter 4, Loading up – Mobile Pentesting Tools, all we need to do now is turn on the proxy and set the right IP and port number in the wireless or APN settings.
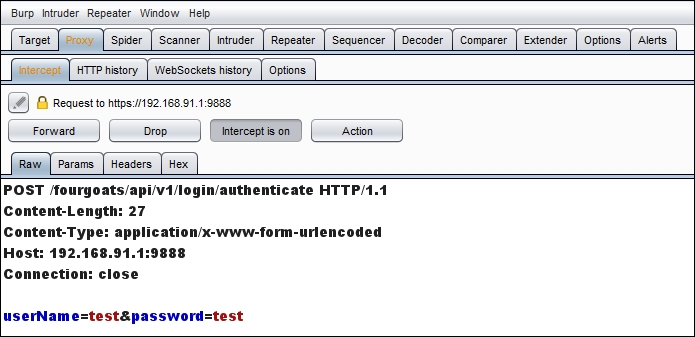
When we launch our target app (FourGoats) and submit the username and password, we should be able to see the request in our proxy tool, as shown in the following screenshot:
Now let's see what changes we can do to the app so that we can manipulate a client-side request to the server. If you try to view your profile, you might receive the request shown in the following screenshot:
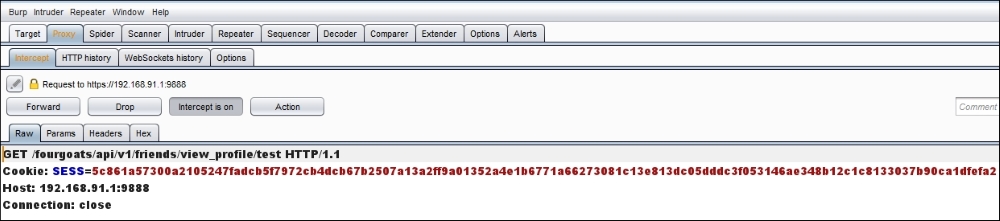
Once the original request is forwarded, the profile of the test user must be displayed...



