Image recovery with Magicrescue
Magicrescue is an older tool that is still very useful, as it quickly scans and recovers certain file types that must be manually specified. For this lab, I’ll be using a 32-GB SanDisk flash drive, which once contained several audio, video, and image files that were all deleted by accident:
- I’ll first run the
fdiskcommand to view the device information by typing the following:sudo fdisk -l
The fdisk command output seen in the following screenshot shows that the flash drive is recognized as sdc2.
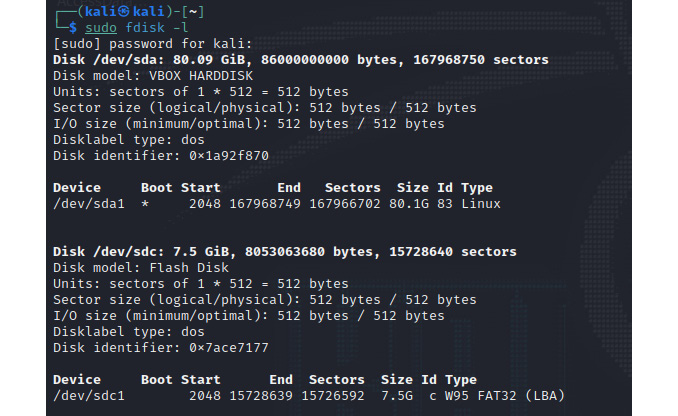
Figure 9.10 – fdisk command output showing disk information
- Before we continue, it is useful to view the magicrescue help manual by typing the following:
man magicrescue
The following figure shows the usage options in magicrescue:
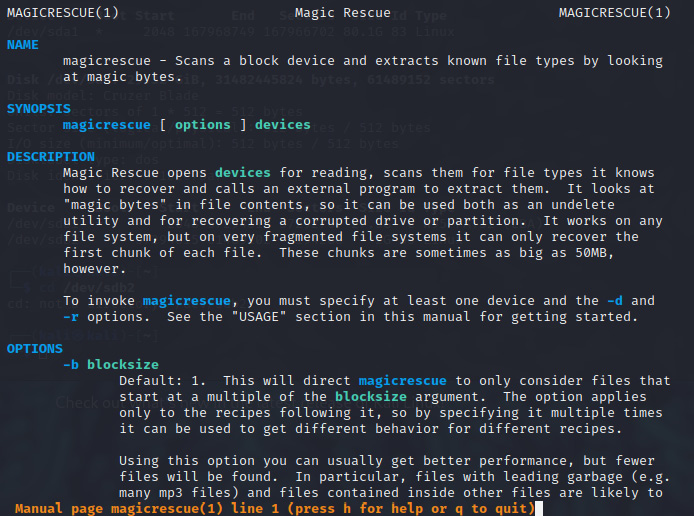
Figure 9.11 – Magicrescue usage options