Wireshark is perhaps one of the best open source packet analyzers available today. Wireshark is a powerful packet analyzer tool, with an easy-to-use, rich GUI and a command-line utility with very active community support: http://ask.wireshark.org.
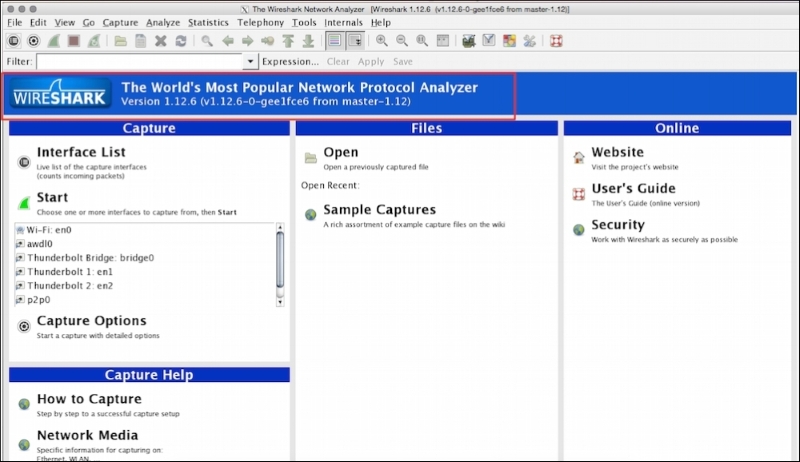
Wireshark uses pcap (libpcap) to capture packets, which means it can capture packets in offline mode—to view the captured packets—and online mode (live traffic) to capture and display the traffic in the Wireshark GUI. Once open, the Wireshark GUI looks like this:
We will see some of the important features that are available in Wireshark in the following figure:
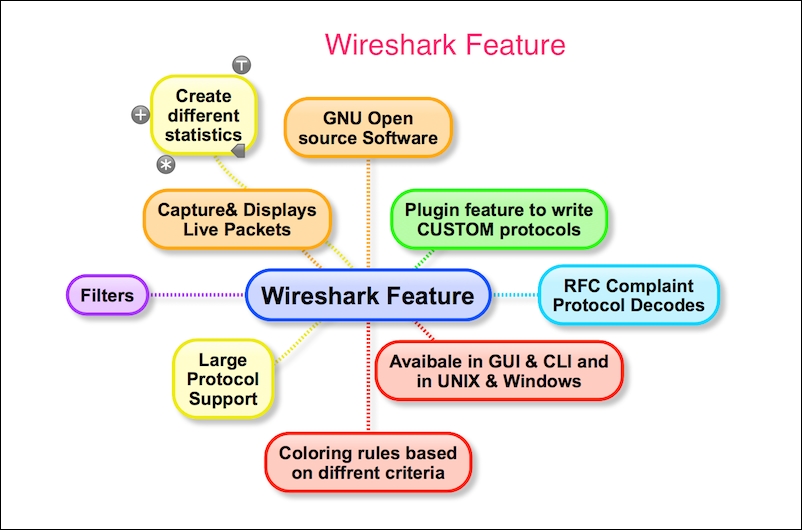
Wireshark has the following cool built-in features, few of them are listed as follows:
Ability to capture live packets from various types of interface
Filters packets with many criteria
Ability to decode larger sets of protocols
Can save and merge captured packets
Can create various statistics
User-friendly GUI and command-line interface
Active community support (http://ask.wireshark.org)
The Wireshark installation provides some command-line tools such as
dumpcap and tshark. Wireshark and tshark rely on dumpcap to capture traffic; more advanced functionality is performed by tshark. Also note that dumpcap can be run as its own standalone utility. tshark is a command-line version of Wireshark and can be used in the remote terminal.
The user must be aware of where Wireshark is installed and it should be obliged with your organization policy before start capturing on the TAP (Test Access Point) or Switch Port Analyzer (SPAN) port.
Usually developers install Wireshark on their personal laptop/desktop and capture packets, which goes in-out from the box.
Certain guidelines should be followed to perform this:
Make sure you're allowed to do what you're going to do; check your corporate policies before capturing a packet.
The operating system must support packet capturing:
Linux packet socket support is enabled in the kernel by default
Windows requires
WinPCapto be installed
Choose the interface and enable the promiscuous mode on it. Promiscuous mode accepts all packets whether they are addressed to the interface or not.
If using a Wi-Fi interface, enable the monitor mode for WLAN capturing.
Start capturing and use Wireshark's different features like (filters/statistics/IO/save) for further analysis