With the improvement of the Windows servicing stack, the possibilities of in-place upgrades got faster and more robust. In-place upgrades aren't the go-to solution, but will do well for a large number of scenarios. Performing an in-place upgrade will preserve all data, settings, apps, and drivers so, it will reduce a huge part of the complexity of migration, transfer of user profile, and (re-)installation of programs.
A big benefit of performing an in-place upgrade is 100% rollback in case of failure. With a classic wipe and load, if there is something wrong after installation, the user ends up with nothing, putting a high time pressure on IT to solve the problem. Mostly, this pressure results in a fast workaround of reinstalling the client a second time and losing all data, settings, apps, and so on.
When something goes wrong during an in-place upgrade, it will completely roll back to its original OS and the user will still be able to work with their client. This gives IT some time to inspect what went wrong and try again later when they have a fix. Even after a successful upgrade, IT has the ability to roll back to the old OS for 10 days if something else is not working as expected.
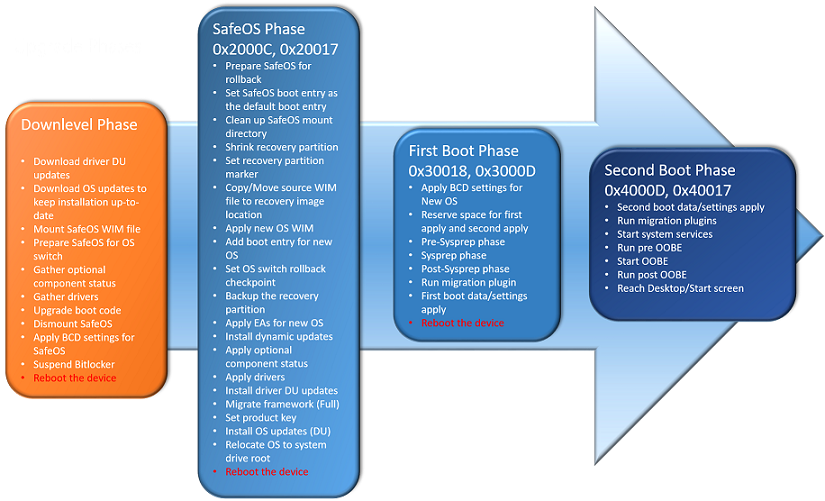
The current in-place upgrade process is divided into four phases, with multiple reboots in between:
- The Downlevel Phase: Depending on whether you are executing setup.exe or executing this phase by upgrading via Windows Update or WSUS, the GUI will be different. But technically, the following steps always need to be done:
- Build a $Windows.~BT folder, analyzing the system and downloading required cumulative updates (if not restricted by setup flags)
- Extract required drivers from the running system or (if not prohibited by setup flags) download drivers from Windows Update
- Prepare the system and the sources, place a SafeOS Windows Preinstallation Environment (PE) boot environment, upgrade the boot entry, and suspend BitLocker (if running)
You will see this phase as Windows Update preparing your system, counting from 0% to 100%. The system will reboot after this phase. Setup result error codes (the second code after the 0xC19xxxxx code) in this phase typically start with 0x100.
- The SafeOS Phase: In this phase, a Windows PE instance is running, which is why it is called so. The recovery partition will be prepared and updated, the old OS will move offline to Windows.old, a new Windows folder will be built, and the new OS WIM will be applied to the drive. Dynamic updates and OS updates will now be installed. After that, the required drivers will be integrated so the system can boot from the new Windows version next time. You will see this phase in older Windows 10 releases as a black screen with a grey ring, like doing a setup installation and in releases since 1607 as a blue screen, like installing Windows Updates, with a message stating part 1 of 3 and counting from 0% to around 30%. The system will reboot after this phase. Setup result error codes (the second code after the 0xC19xxxxx code) in this phase typically start with 0x2000C or 0x20017.
- The First Boot Phase: Now the new system will boot up for the first time and run through the sysprep phase. Device drivers are getting ready and the migration plugin is running to extract all required data from the old OS. Already, the first boot data and settings have been applied. You will see this phase as part 2 of 3 and counting from 30% to 60%. The system will reboot after this phase. Setup result error codes (the second code after the 0xC19xxxxx code) in this phase typically start with 0x30018 or 0x3000D.
- The Second Boot Phase: In this last phase, the system runs the migration plugin one last time, applies the last migrated settings, starts the system services, and runs the Out of Box Experience (OOBE) phase. You will see this phase as part 3 of 3 and counting from 60% to 100%. The system will present you with the login screen after this phase. Setup result error codes (the second code after the 0xC19xxxxx code) in this phase typically start with 0x4000D or 0x40017.
The in-place upgrade process can only exchange your OS files. Therefore, it is only allowed to use a base ISO/WIM including only the operating system. The use of a sysprepped or so-called golden system with additional apps included in the WIM is not supported. Microsoft could have designed a way around it to handle other Microsoft products such as Office. But this would end up in a two-class citizen system. So the decision was made to only support the pure base OS upgrade.
Only use an original WIM from MSDN or VLSC center. You are allowed to and it is recommended you service these WIMs with the newest cumulative update offline. To reduce unnecessary growth of the WIM file, start over each time with the original WIM.
With this move of Windows to Windows.old and a complete rebuild of the new OS, only migrating the required settings, apps, and drivers, the whole process is now very robust and prevents too much waste from older OSes. Even so, Microsoft does not provide detailed numbers. We could observe only very low numbers of rollback at approximately 2%-5% in huge national and international customers. And even if a rollback occurs, the system is still usable.
This in-place upgrade process runs smooth and fast on modern hardware. We clocked approximately 17 minutes on a Surface Book i7 with 256 GB NVMe and 60-70 apps installed. Even on a 3 or 4-year-old i5-class system with an SSD, times of approximately 25 minutes were possible. On very old hardware with low-RPM HDDs and a low amount of RAM, installation times can grow up to 1 hour 30 minutes and more.
 Free Chapter
Free Chapter