In this section, we'll take a look at the following subtopics:
Now, let's get some packets to work with. I'm going to start a quick capture.
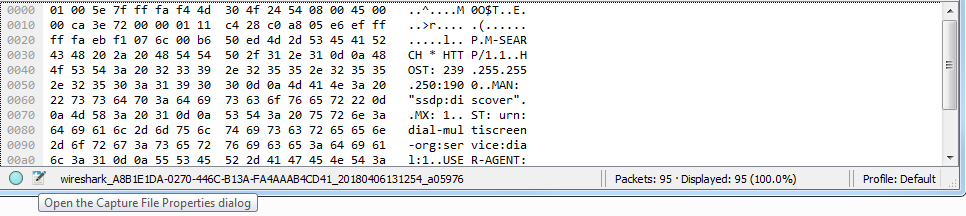
To create comments for a packet capture, the entire capture itself, you can do so in the bottom left-hand corner of Wireshark. You see there are two icons down there: one's a circle icon called the expert information we'll get into in a future section, and there's a pencil with a packet capture icon. If you do a mouseover on a pencil icon, it'll say Open the Capture File Properties dialog:
Click on that and it will open up a pop-up window that gives you a bunch of different information for the capture itself. And there's a bottom section here that says File Comment, and here you can enter whatever sort of description you want for the entire packet capture. So maybe...



