In this section, we'll take a look at how ICMP is useful to network engineers and what some of the different types of ICMP are and what they mean.
The first thing we will do is create some ICMP packets. For that we will create a ping request, which is a type of ICMP.
So, let's go ahead and start the capture, and we'll go ahead and ping Google again:

Each one of the replies is a series of ICMP requests and responses.
Stop the capture and we'll apply an icmp display filter:
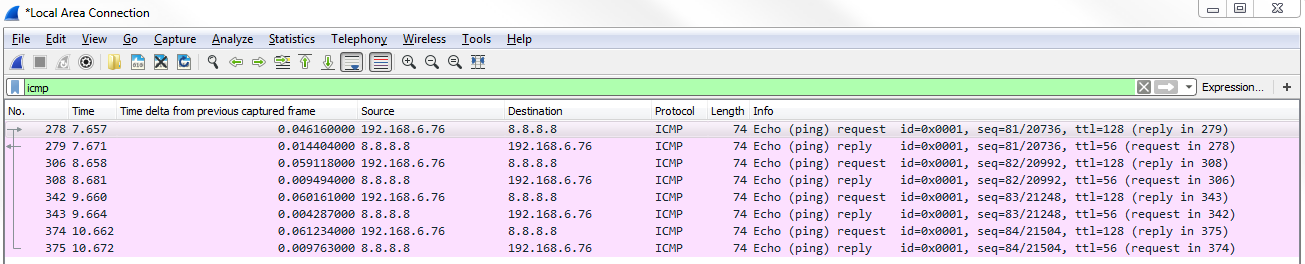
As shown in the preceding screenshot, these are all of my ICMP packets that have been sent and received, and we can see that we have multiple requests and replies. This coincides with the four replies that we saw in the command line.
If we dive into the header, by going down to the very bottom in the packet details—that is, to Internet Control Message Protocol, we can see that we have Type and Code:

Type and Code are the two important parts within ICMP. We see we have Type 8: (Echo (ping) request). Then, in the next...



