In this section, we'll take a look at how DHCP works, some of the fields that are within the DHCP protocol, watch a client retrieve an IP address, and also take a look at what happens with DHCP when a client requests an address and receives responses.
Let's start a packet capture. What we'll do now is release the address on my computer and then renew it.
Type ipconfig /release on a Windows computer on Command Prompt to release our address, then if we type ipconfig /renew, it will get us a new address.
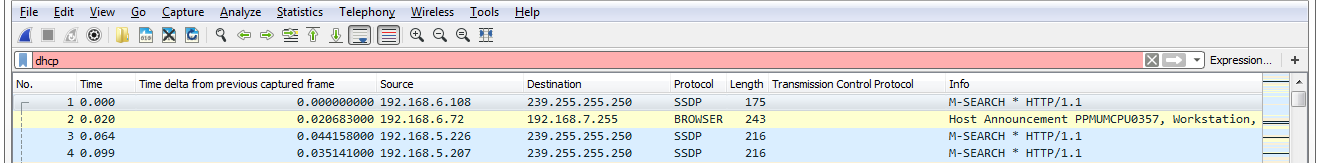
Now, if we type ipconfig /all, we should be able to see that our address is assigned. We'll stop our capture now. We'll want to only pick out the DHCP traffic. So you would assume you could go up to the display filter and type dhcp, just like we've done for the other protocols, and then press Enter and it works. But we can see that there's a red bar up there, which indicates that dhcp is not valid:
This is because the display filter is actually bootp. DHCP is based off of bootp. bootp...



