-
Book Overview & Buying

-
Table Of Contents

CompTIA CySA+ Study Guide: Exam CS0-002
By :

 Sign In
Start Free Trial
Sign In
Start Free Trial


THE COMPTIA CYBERSECURITY ANALYST+ EXAM OBJECTIVES COVERED IN THIS CHAPTER INCLUDE:
 Chapter 5, “Building an Incident Response Program,” provided an overview of the steps required to build and implement a cybersecurity incident response program according to the process advocated by the National Institute of Standards and Technology (NIST). In their Computer Security Incident Handling Guide, NIST outlines the four-phase incident response process shown in Figure 8.1
Chapter 5, “Building an Incident Response Program,” provided an overview of the steps required to build and implement a cybersecurity incident response program according to the process advocated by the National Institute of Standards and Technology (NIST). In their Computer Security Incident Handling Guide, NIST outlines the four-phase incident response process shown in Figure 8.1
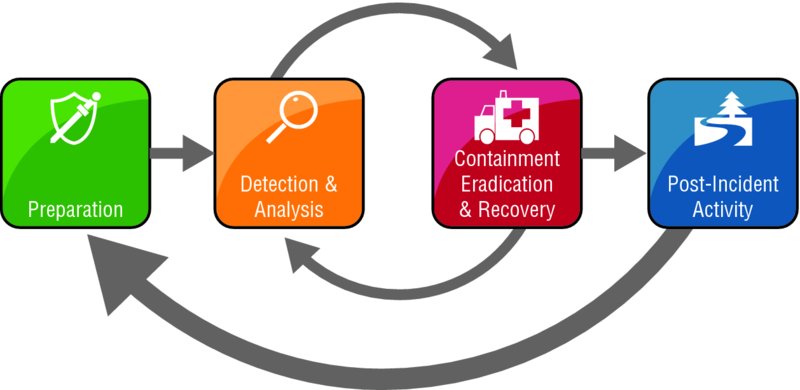
Figure 8.1 Incident response process
Source: NIST SP 800-61: Computer Security Incident Handling Guide
The remainder of Chapter 5 provided an overview of the Preparation phase of incident response. Chapter 6, “Analyzing Symptoms for Incident Response,” and Chapter 7, “Performing Forensic Analysis,” covered the details...

Change the font size
Change margin width
Change background colour