Antivirus bypass in a nutshell
In order to prove the central claim of this book, that antivirus software cannot protect the user completely, we decided to conduct research. Our research is practically tested based on our written and compiled EXE files containing code that actually performs the techniques we will explain later on, along with payloads that perform the bypass. The goal of this research wasn't just to obtain a shell on the endpoint, but rather to actually control it, transmit remote commands, download files from the internet, steal information, initiate processes, and many more actions – all without any alert from the antivirus software.
It is important to realize that just because we were able to bypass a particular antivirus software, that does not mean that it is not good software or that we are recommending against it. The environment in which the antivirus software was tested is a LAN environment and it is entirely possible that in a WAN environment, the result might have been different.
The communication between the malware and the C2 server was done using the TCP protocol in two ways:
- Reverse shell
- Bind shell
The difference between these two methods lies in how communication is transmitted from the malware to the attacker's C2 server. Using the method of the bind shell, the malware acts as a server on the victim endpoint, listening on a fixed port or even several ports. The attacker can interact with the endpoint using these listening port(s) at any time the malware is running.
Using the reverse shell method, the listening fixed port will be open on the attacker's C2 server and the malware acts as a client, which in turn will connect to the attacker's C2 server using a random source port that is opened on the victim endpoint.
The following diagram demonstrates the differences between reverse and bind shell:
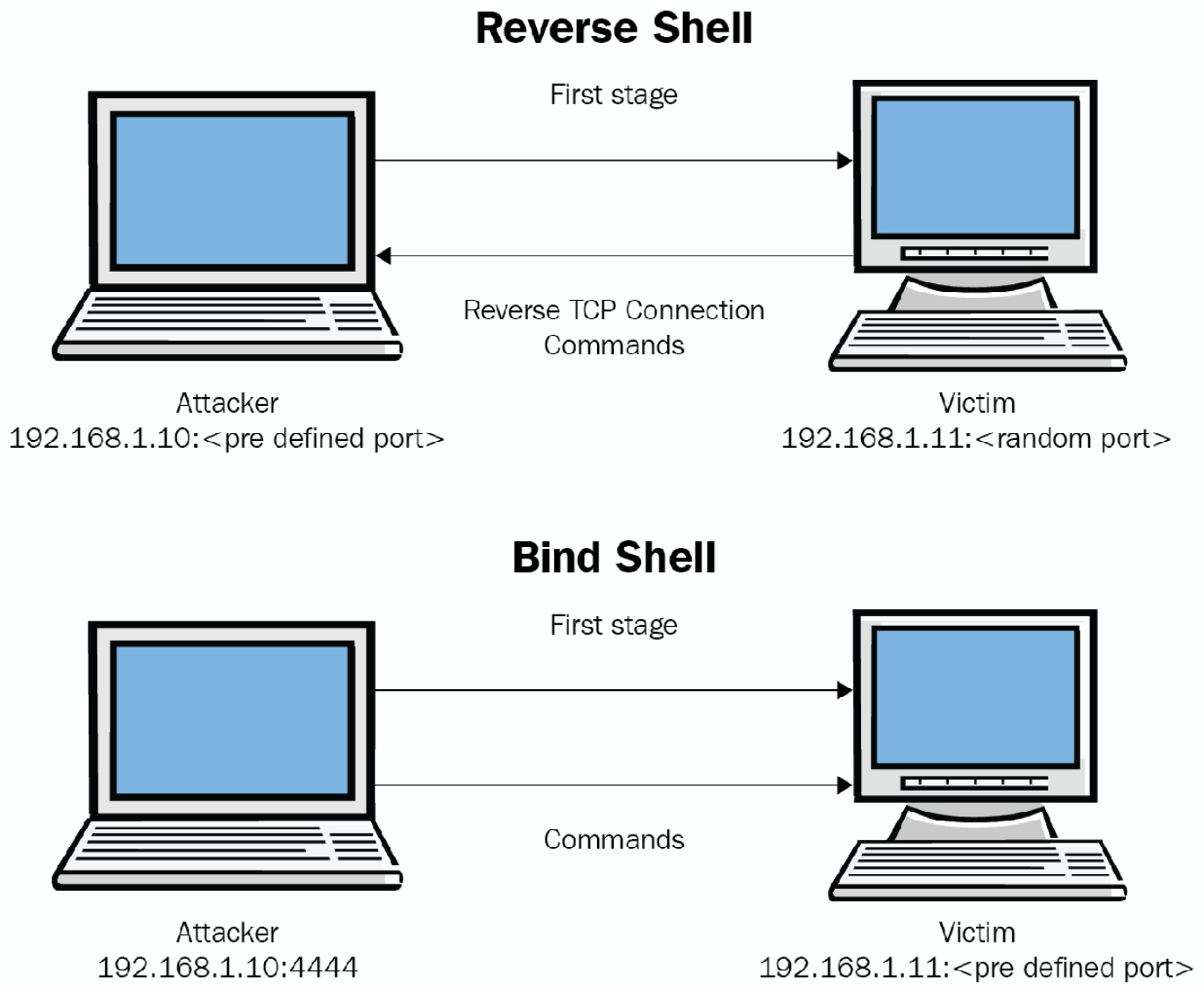
Figure 1.4 – Reverse shell and bind shell
Most of the time, threat actors will prefer to base their malicious payload to interact with their C2 servers on the reverse shell technique. This is because it is relatively easy to implement; it will work behind Network Address Translation (NAT) and it will probably have the chance to fool antivirus software and firewall solutions.



