Scanning a web app passively
Passive scanning is constantly running and recording findings in the background of the ZAP Proxy. It works by combing through traffic that passes into the ZAP Proxy. This is a passive background thread that does not affect the performance of an application because it scans traffic stored already on ZAP.
Getting ready
For this recipe, all you need to do is start and run ZAP.
How to do it…
When opening Tools | Options, scroll down on the left side until you see Passive Scanner. Here, you will have the configuration option checkboxes, asking you first whether only in-scope messages should be scanned and include traffic from the fuzzers. The last two options are for editing the maximum number of alerts per rule that can be raised and the maximum body size in bytes to scan on the application.
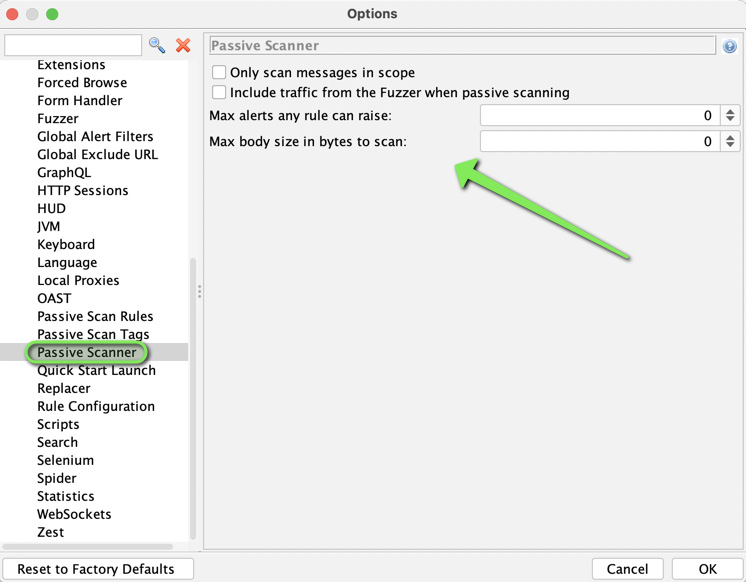
Figure 3.17 – The Passive Scanner options
Tip
For the shortcut hotkey, click and hold Ctrl + Alt and then press...