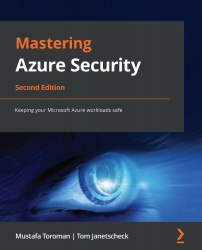
Exploring the shared responsibility model
While Microsoft Azure is very secure, the responsibility for building a secure environment doesn't rest with Microsoft alone. Its shared responsibility model divides responsibility between Microsoft and its customers.
Before we can discuss which party looks after which aspect of security, we need to first discuss cloud service models. There are three basic models:
- Infrastructure as a Service (IaaS)
- Platform as a Service (PaaS)
- Software as a Service (SaaS)
These models differ in terms of what is controlled by Microsoft and the customer. A general breakdown can be seen in the following diagram:
Figure 1.1 – Basic cloud service models
Let's look at these services in a little more detail.
On-premises
In an on-premises environment, we, as users, take care of everything: the network, physical servers, storage, and so on. We need to set up virtualization stacks (if used), configure and maintain servers, install and maintain software, manage databases, and so on. Most importantly, all aspects of security are our responsibility: physical security, network security, host and OS security, and application security for all application software running on our servers.
IaaS
With IaaS, Microsoft takes over some of the responsibilities. We only take care of data, runtime, applications, and some aspects of security, which we'll discuss a little later on.
An example of an IaaS product in Microsoft Azure is Azure Virtual Machines (VM).
PaaS
PaaS gives Microsoft even more responsibility. We only take care of our applications. However, this still means looking after a part of the security. Some examples of PaaS in Microsoft Azure are Azure SQL Database and web apps.
SaaS
SaaS gives a large amount of control away, and we manage very little, including some aspects of security. In Microsoft's ecosystem, a popular example of SaaS is Office 365; however, we will not discuss this in this book.
Now that we have a basic understanding of shared responsibility, let's understand how responsibility for security is allocated.
Division of security in the shared responsibility model
The shared responsibility model divides security into three zones:
- Always controlled by the customer
- Always controlled by Microsoft
- Varies by service type
Irrespective of the cloud service model, customers will always retain the following security responsibilities:
- Data governance and rights management
- Endpoint protection
- Account and access management
Similarly, Microsoft always handles the following, in terms of security, for any of its cloud service models:
- Physical data center
- Physical network
- Physical hosts
Finally, there are a few security responsibilities that are allocated based on the cloud service model:
- Identity and directory infrastructure
- Applications
- Network
- Operating system
The distribution of responsibility, based on different cloud service models, is shown in the following diagram:

Figure 1.2 – The distribution of responsibility between the customer and service provider for different cloud service models (image courtesy of Microsoft, License: MIT)
Now that we know how security is divided, let's move on to one specific aspect of it: the physical security that Microsoft manages. This section is important as we won't discuss it in much detail in the chapters to come.