Now that we know more about the threats, it's even more important for you to know where to access information about these vulnerabilities. You also need to be aware of any resources that are available so that you can educate yourself on what's required to remediate any vulnerabilities. As you are already aware, Windows is renowned for its ongoing vulnerabilities, and patching/updating these systems has morphed into a full-time and very specialized role over the years. The following website is the authoritative source with regard to Microsoft security updates: https://portal.msrc.microsoft.com/en-us/security-guidance.
Useful information
Here is the link to the Microsoft Security Response Center (MSRC): https://www.microsoft.com/en-us/msrc?rtc=1.
As shown in the following screenshot, you will be provided with a list of all identified vulnerabilities from Microsoft within a selected time range with additional filtering options. To give you an idea of the risk profile for Windows, the following filter is scoped to Windows 10 for x64-based systems over the last month, which returned 47 uniquely addressed vulnerabilities:
Figure 1.4 – Microsoft Security Update Guide
One term you may have heard as part of vulnerability management with Microsoft is the famous Patch Tuesday (also referred to as Update Tuesday). Patch Tuesday occurs on the second Tuesday of every month and is the day that Microsoft releases its monthly patches for Windows and other Microsoft products. There are many references on the internet for Patch Tuesday in addition to the MSRC. One example of a common resource used to track Patch Tuesday releases is the Patch Tuesday Dashboard: https://patchtuesdaydashboard.com/. Another example to better manage your notifications when vulnerabilities are released is PatchManagement.org: http://patchmanagement.org/.
As you review the updates needed for your Windows systems, you will notice that each of them has a unique identifier to reference the update beginning with CVE®. CVE stands for Common Vulnerabilities and Exposures and is the standard for vulnerability management, allowing one source to catalog and uniquely identify vulnerabilities. CVE is not a database of vulnerabilities but a dictionary providing definitions for vulnerabilities and exposures that have been publicly disclosed. The U.S. Department of Homeland Security (DHS) and the Cybersecurity and Infrastructure Security Agency (CISA) sponsor the CVE.
Tip
Visit this website to learn more about CVE: https://cve.mitre.org/about/index.html.
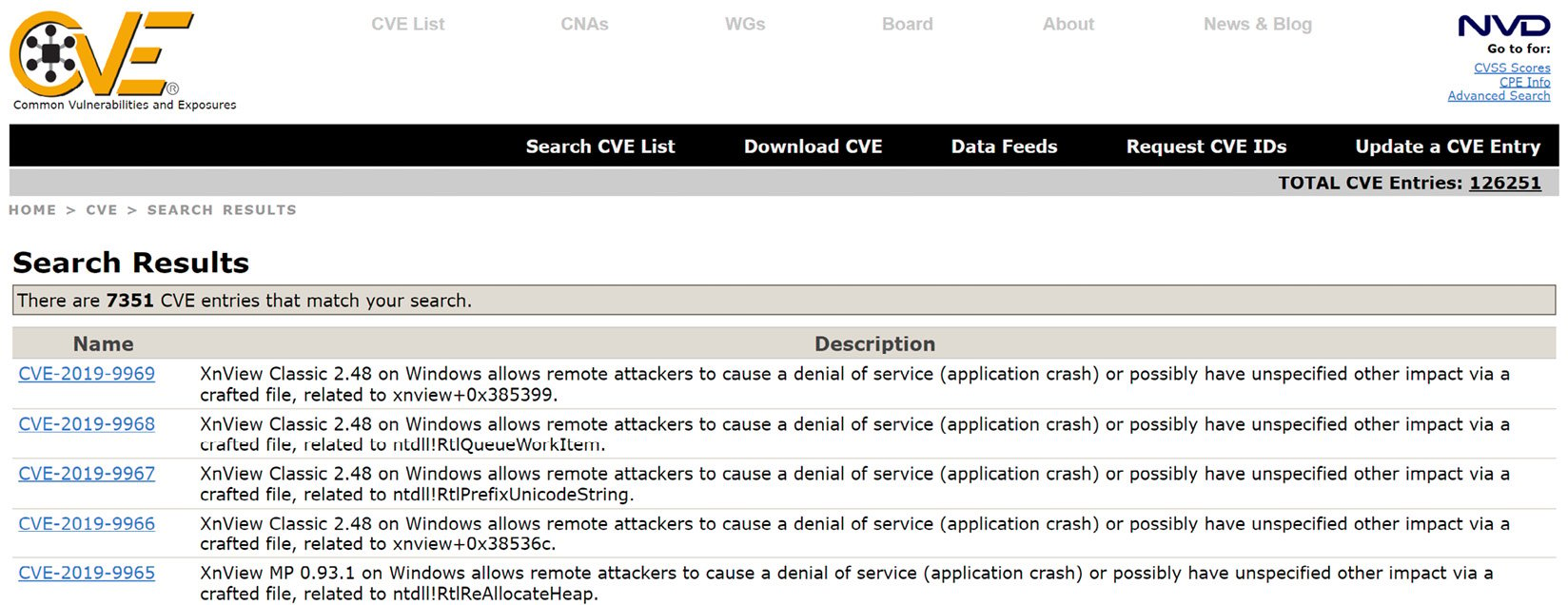
The following screenshot shows an overview of what the CVE provides and can be found at https://cve.mitre.org/cgi-bin/cvekey.cgi?keyword=Windows:
Figure 1.5 – CVE® Windows Search Results
In addition to the CVE there's the NVD. The NVD is the National Vulnerability Database, which is an additional resource for vulnerability management provided by NIST. The NVD is synced with the CVE to ensure the latest updates appear within its repository. The NVD provides additional analysis of the vulnerabilities listed in the CVE dictionary by using the following:
- Common Vulnerability Scoring System (CVSS) for impact analysis
- Common Weakness Enumeration (CWE) for vulnerability types
- Common Platform Enumeration (CPE) for a structured naming standard
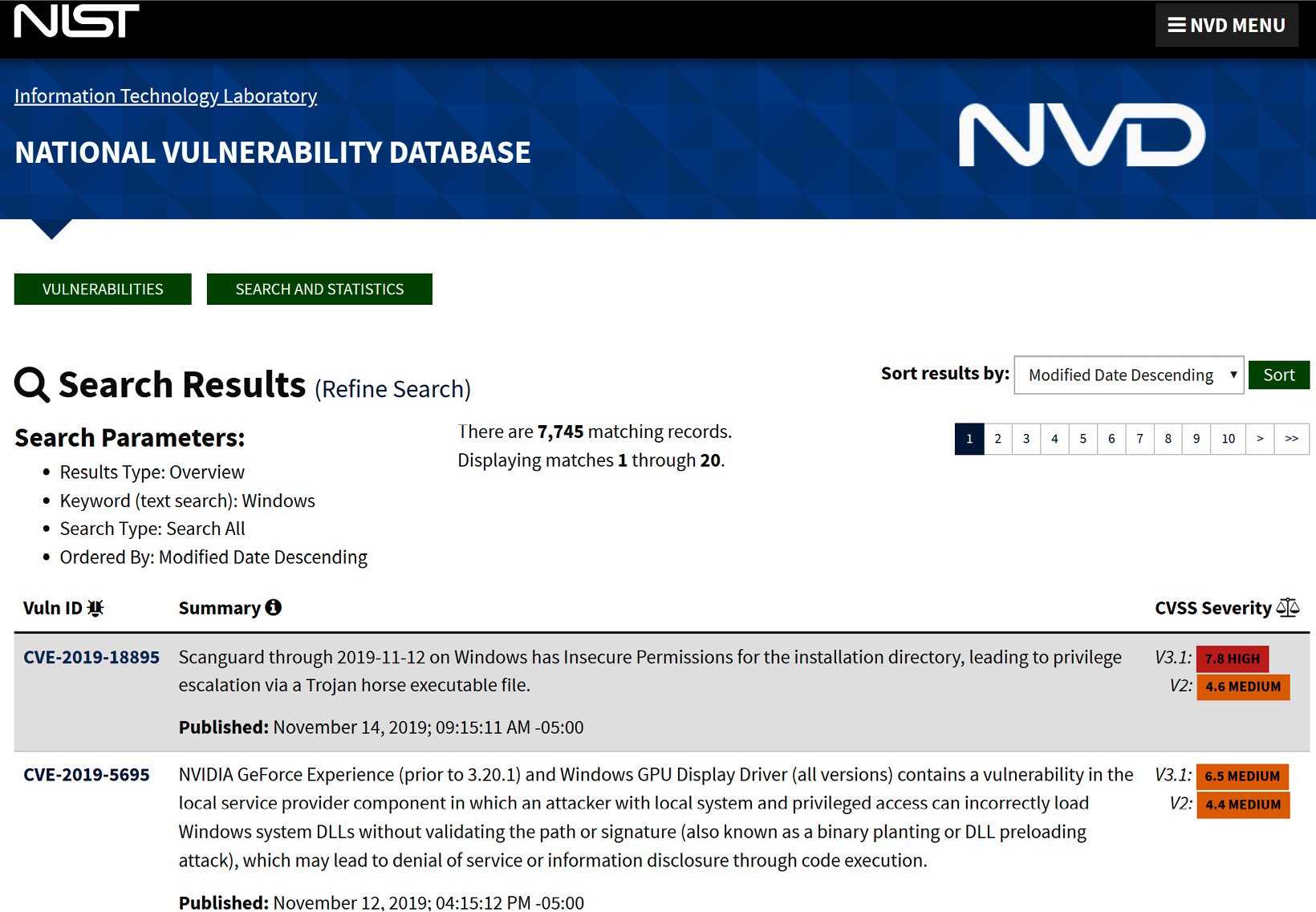
The following screenshot shows an overview of what the NVD provides and can be found via https://nvd.nist.gov/vuln/search/results?form_type=Basic&results_type=overview&query=Windows&search_type=all:
Figure 1.6 – NVD Windows Search Results
One additional resource that we should mention is the Open Web Application Security Project (OWASP). OWASP is a nonprofit organization to help improve the security of software for individuals and enterprises. They provide a tremendous amount of resources such as tools, documentation, and a community of professionals all looking to continually enhance software security. Although application and web-specific, there is a high possibility that the application or web app will be running on both your Windows server and Windows client. Because of this, it is critical, as a security professional, for you to be able to intelligently discuss these concerns and challenges with the business, developer(s), and application/web app owners.
Tip
You can find more information about OWASP at https://www.owasp.org/index.php/Main_Page.
One of the more common projects that OWASP provides is the OWASP Top 10, which provides the most critical web application security risks. The latest version available was published in 2017 and is presented here:
- Injection
- Broken authentication
- Sensitive data exposure
- XML External Entities (XXE)
- Broken access control
- Security misconfiguration
- Cross-Site Scripting (XSS)
- Insecure deserialization
- Using components with known vulnerabilities
- Insufficient logging and monitoring
Tip
View OWASP Top 10 2017 – The Ten Most Critical Web Application Security Risks here: https://owasp.org/www-project-top-ten/OWASP_Top_Ten_2017/.
 Free Chapter
Free Chapter