Fat binaries (also known as multi-architecture binaries or universal binaries) are quite unique, as they are used to store code for several different architectures. The format includes a custom fat header, followed by a set of Mach-O files:

Figure 2: A fat Mach-O executable file
Here is the header structure:
struct fat_header {
unsigned long magic; /* FAT_MAGIC */
unsigned long nfat_arch; /* number of structs that follow */
};
The magic value, in this case, is 0xcafebabe.
This header is followed by several fat_arch structures, whose amount is equal to the value specified by the nfat_arch field:
struct fat_arch {
cpu_type_t cputype; /* cpu specifier (int) */
cpu_subtype_t cpusubtype; /* machine specifier (int) */
unsigned long offset; /* file offset to this object file */
unsigned long size; /* size of this object file */
unsigned long align; /* alignment as a power of 2 */
};
All these structures can be found in the officially published Apple source code:
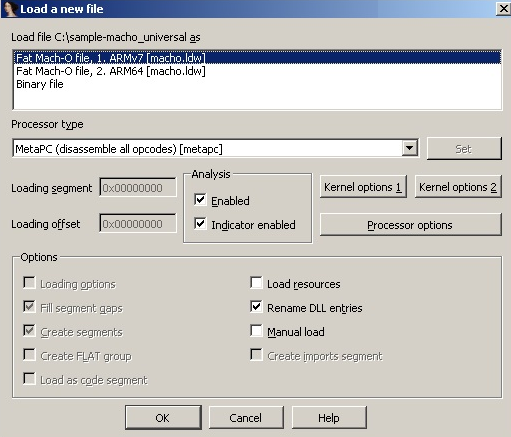
Figure 3...



