OllyDbg UI interface is pretty simple and easy to learn. Here, will cover the steps and the different windows that can help you through your analysis:
- Select a sample to debug: You can directly open the sample file from File | Open and choose a PE file to open (it could be a DLL file as well, but make sure it's a 32-bit sample). Or, you can attach to a running process as follows:
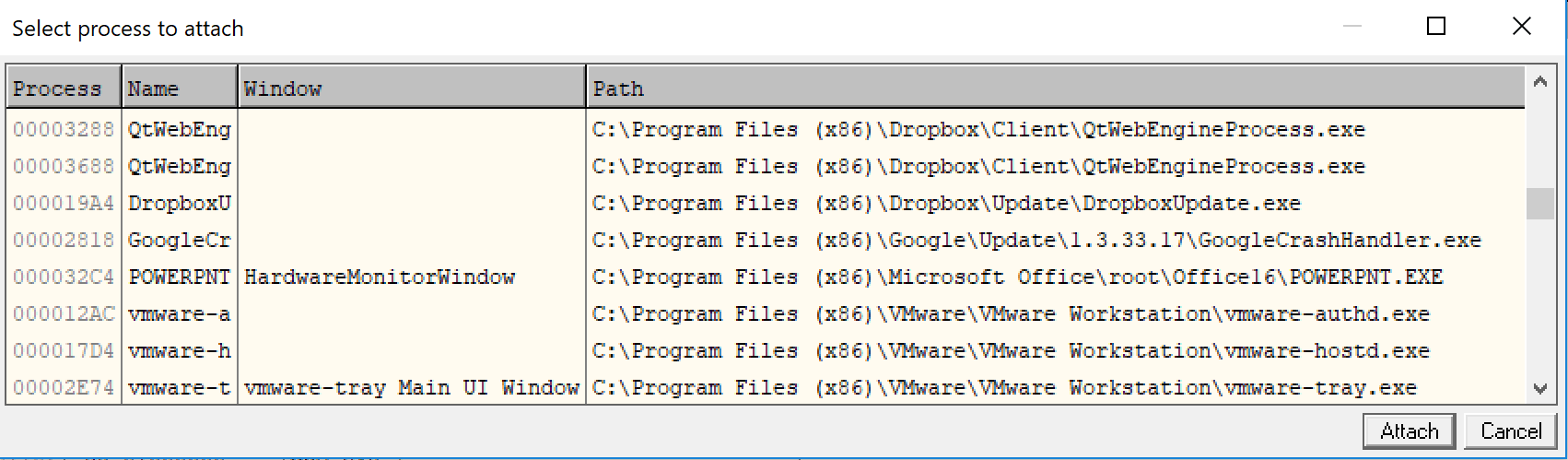
Figure 18: OllyDbg attaching dialog window
- CPU window: Your main window: This is the window that you spend most of your debugging time in. This window includes the assembly code on the top-left side and provides an option set breakpoints by double-clicking on the address or modifying the program's assembly code.
You've also got the registers on the top-right side and you have the ability to modify the registers at any given time (if the execution is paused). At the bottom side you have the stack and the data in hex, which you can also modify.
You can simply...



